Like sharks off the coast of North Carolina this summer, information security threats are lurking. And now that cloud computing is woven into the fabric of IT everywhere, specific risks to an enterprise’s data apply.
Cloud computing is to IT what Shark Week is to summertime: a cultural feeding frenzy. In a nod to the annual TV chomp-fest, Perspecsys presents the Seven Cloud Security Mistakes Bound to Bite You.
But taking basic precautions – whether at the beach or on the job – can help keep you and your data safe, respectively.
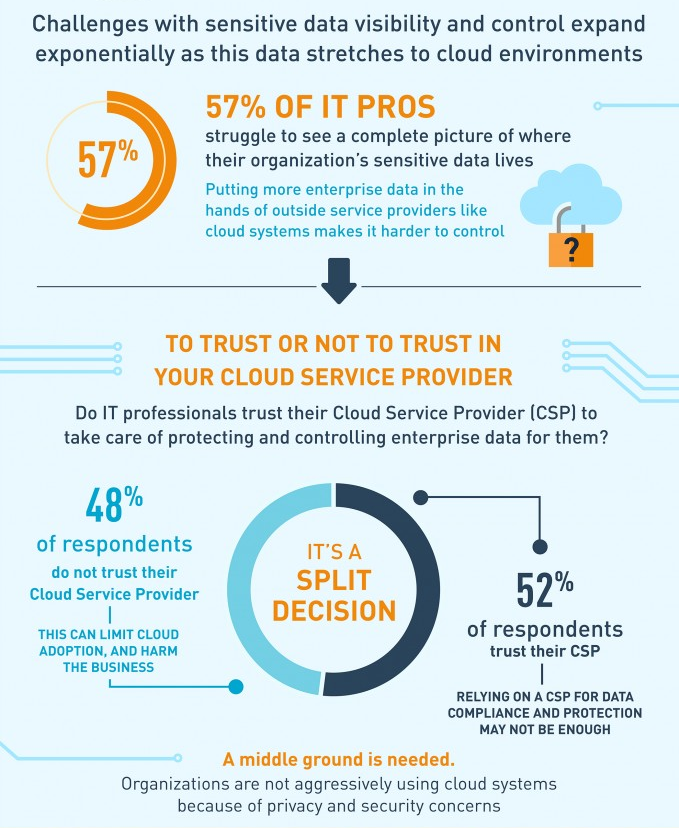
Just as swimmers are at the mercy of the ocean, using public cloud services equates to turning control of your data – even the sensitive and regulated data – over to cloud Service Providers.
Safety tip: For users: adhere to IT and security policies set by your organization when signing up for cloud services for business use. For organizations: Get familiar with data-centric security tools that work in and outside the company’s walls, in particular, cloud data encryption and tokenization.
There are some beaches were you know you should not be going into the water. In the same vein, knowing the physical locations of where your data is being processed and stored will keep you on the right side of data-residency regulations that have a painful bite if they are violated.
Safety tip: Make sure you understand where you cloud provider’s primary and back-up datacenters are located. Take time to investigate the prevailing legal requirements in all of these jurisdictions regarding data privacy. Look to technologies such as cloud data tokenization to keep data resident in specific locations if data residency issues are challenging your cloud adoption program.
When you sign up for cloud apps, you agree to the associated terms and conditions. This is like going full Hasselhoff with disregard for beach warning signs, since the policies and standards your organization adheres to regarding the treatment of data are likely not shared by the cloud service provider.
Safety tip: Insist on contractual clauses, which require that data maintained by your service providers be treated in certain ways. For example, if regulated data such as patient information is placed in third party cloud systems, additional safeguards may need to be put in place to ensure it is adequately protected.
Weak passwords are like a three-sided shark cage. Cyber criminals can swim right through your defenses. The top 100 passwords people use haven’t changed over the years, according to Researcher Mark Burnett who released 10 million passwords collected from data breaches over the past decade.
Safety tip: Use different passwords for different services and change your passwords frequently.
Letting passwords lull you into a false sense of security is like thinking you’re safe by swimming in a group, but not knowing there’s a colony of seals a few feet away. Shark and cyber attacks are both on the rise in 2015 as the number of bites and breaches continue to climb. The good news is that awareness is rising that even a strong password isn’t enough to keep data safe and savvy professionals are putting multiple layers of defense in place.
Safety tip: Strong multi-factor authentication is necessary to keep the network and cloud applications secure. Also use techniques like data encryption and tokenization to minimize the number of systems where data flows to in the “clear”, thereby minimizing the points where cyber criminals can get their hands on anything meaningful.
Boating without a life raft isn’t a high percentage move in the event of an accident. If anything, the famous U.S.S. Indianapolis speech from Jaws will make you want to always have a back up ride to shore. Make sure your cloud provider allows you to make local backups of your data too. This isn’t always possible with some of the big consumer cloud services, so be sure to ask.
Safety tip: Having backups of your data is always a good idea whether it is stored in the cloud or not. Using more than one cloud service minimizes the risk of widespread data loss or downtime due to a localized component failure.
If only Quint had listened to Chief Brody and went back to shore to get a bigger boat, perhaps he would have survived! As with most things in life, incorporating new data points into your plans can help keep you afloat. As you consider your cloud adoption programs, stay abreast of impending changes that can impact your cloud use, such as data privacy regulations that have been getting increasingly strict over the past year.
Safety tip: Map out the “life” of your cloud data. Pay attention to what countries it flows through and where it gets processed and stored. Identify if the movement of your data to any of these countries creates potential compliance or regulatory issues for you – either now or in the future – and take proactive steps to address the problem before it is too late.
By David Canellos
David is President and CEO of Perspecsys. Previously, David was SVP of Sales and Marketing at Irdeto Worldwide, a division of Naspers. Prior to that, David was the President and COO of Cloakware, which was acquired by Irdeto. Before joining Cloakware, David was the General Manager and Vice President of Sales for Cramer Systems (now Amdocs), a UK-based company, where he was responsible for the company’s revenue and operations in the Americas.





