In just a few years, information technology has quickly evolved into an indispensable and central part of our lives. Both personally and business-wise, those few who don’t rely on technology are either so far outside of civilizations that access is impossible or believed by the rest of us to be perplexingly eccentric. But just as these tools and services so integral to our lives have developed, so too has the dark side of technology progressed.
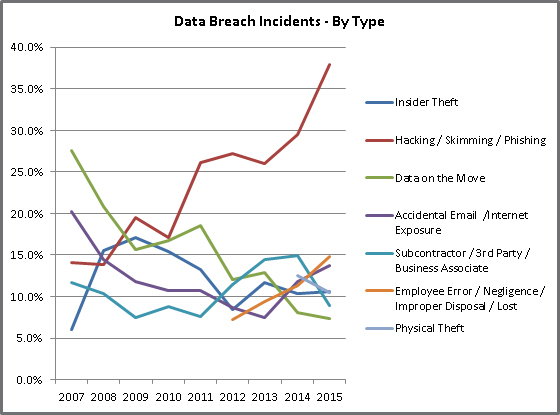
In February this year, hackers attempted to steal $951 million from the Bangladesh Central Bank; though the majority of the transactions were prevented, $81 million was lost to the Philippines and authorities have yet to track the responsible parties. But hackers aren’t interested only in financial gain. According to the Identity Theft Resource Centre (ITRC), 2015 saw 781 tracked data breaches in the US, the second highest record since the ITRC began tracking in 2005. Says Eva Velasquez, President and CEO of ITRC, “While the overwhelmingly prevalent motive for data breaches remains financial gain for the thieves, we saw a shift in new motives for obtaining sensitive and private personal data this year.”
The ITRC 2015 Breach List points to the business sector for nearly 40% of the reported breaches, followed by the healthcare sector at 35.5%, and the financial sector at 9.1%. Some of the famed breaches of 2015 include the CareFirst BlueCross BlueShield breach which pointed to vulnerabilities of the healthcare industry, the cyber attack of password management company LastPass compromising email addresses and password reminders, and the violation of health insurer Anthem which exposed 80 million patient and employee records. Though maintaining an extensive database which captures and categorizes US data breaches, the ITRC notes that their reported numbers are probably well below the actual due to many organizations preferring to keep security infringements private, fearing a backlash from investors and other potentially impacted parties.
According to Gartner, by 2017 the average IT organization will spend 30% of its budget on security, risk, and compliance. Further, Gartner predicts that 2020 will see the existence of a black market exceeding $5 billion selling video data and fake sensors, and security costs addressing IoT security will increase to 20% of annual security budgets from only 1% in 2015. Says Ted Friedman, VP and analyst at Gartner, “The IoT has enormous potential to collect continuous data about our environment. The integrity of this data will be important in making personal and business decisions, from medical diagnoses to environmental protection, from commands to modify actions of machinery to identification and authorization of physical access. A black market for fake or corrupted sensor and video data will mean that data can be compromised or substituted with inaccurate or deliberately manipulated data.”
MIRACL, a key player in the internet cyber security space, is attempting to address Vulnerabilities via a new partnership with NTT. CEO Brian Spector discussed the necessity of security with CloudTweaks and states, “The systems, hardware, and methods of security that store personal or operational data (in the case of IoT/connected devices) are all vulnerable if conventional methods are used (digital certificates can be spoofed, username/password databases can be hacked). The best way to prevent a username/password breach is not to store usernames or passwords on a server. And the best way to prevent digital certificates from being spoofed is not to use them to authenticate your site to a user.”
Announced today, Apache Milagro (incubating) is an open source distributed cryptographic platform for cloud computing providing security beyond a single point of trust with distributed key pairings. Says Spector, “What Apache Milagro (incubating) offers is a better way to establish a secure web. No shared secrets. No user ID or passwords needed or stored (eliminating the single largest point of compromise). The M-Pin Protocol is a zero-knowledge authentication protocol meaning that the client can prove to the server that they are in possession of the original secret without having to transmit it to the server.”
Undoubtedly, our security protocols need to develop as fast as, if not faster, than the services we already benefit from; implementing the best security solutions for your organization is crucial.
By Jennifer Klostermann





