The growth of cloud services has been one of the most disruptive phenomena of the Internet era. However, even the most popular cloud services (including Yahoo, Gmail, Microsoft Outlook 365, and Dropbox) are vulnerable to attack because their servers operate on unencrypted data.
The move to cloud-based services offers enormous benefits compared with managing these services in-house. The cloud is scalable, cost-effective, easy to manage, and accessible to a wide range of devices anywhere.
But because cloud services represent a centralized repository of information, they are tempting targets for attackers. If an attacker is successful in breaching a single user’s computer or phone, that user’s information will be compromised. But if an attack targeting a server is successful, information forall users on that server can be leaked. For example, Yahoo recently disclosed that over a billion user accounts were compromised.
Accordingly, the security industry has invested heavily in technologies and processes to protect cloud servers. Many of these – such as firewalls, threat detection and analysis, and administrative processes – amount to “building taller walls” around the server. But despite great effort and investment, attackers continue to prevail.
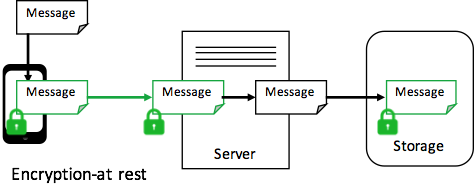
What if the problem is turned around? Instead of figuring out how to protect the server, what if the focus is on protecting the data whether or not the server has been compromised? This can be achieved with end-to-end encryption, which means user data is decrypted only on computers or phones; never on the server. Therefore, if the server is breached an attacker will only be able to access encrypted data, which is unintelligible. Unfortunately, end-to-end encryption is rarely used.
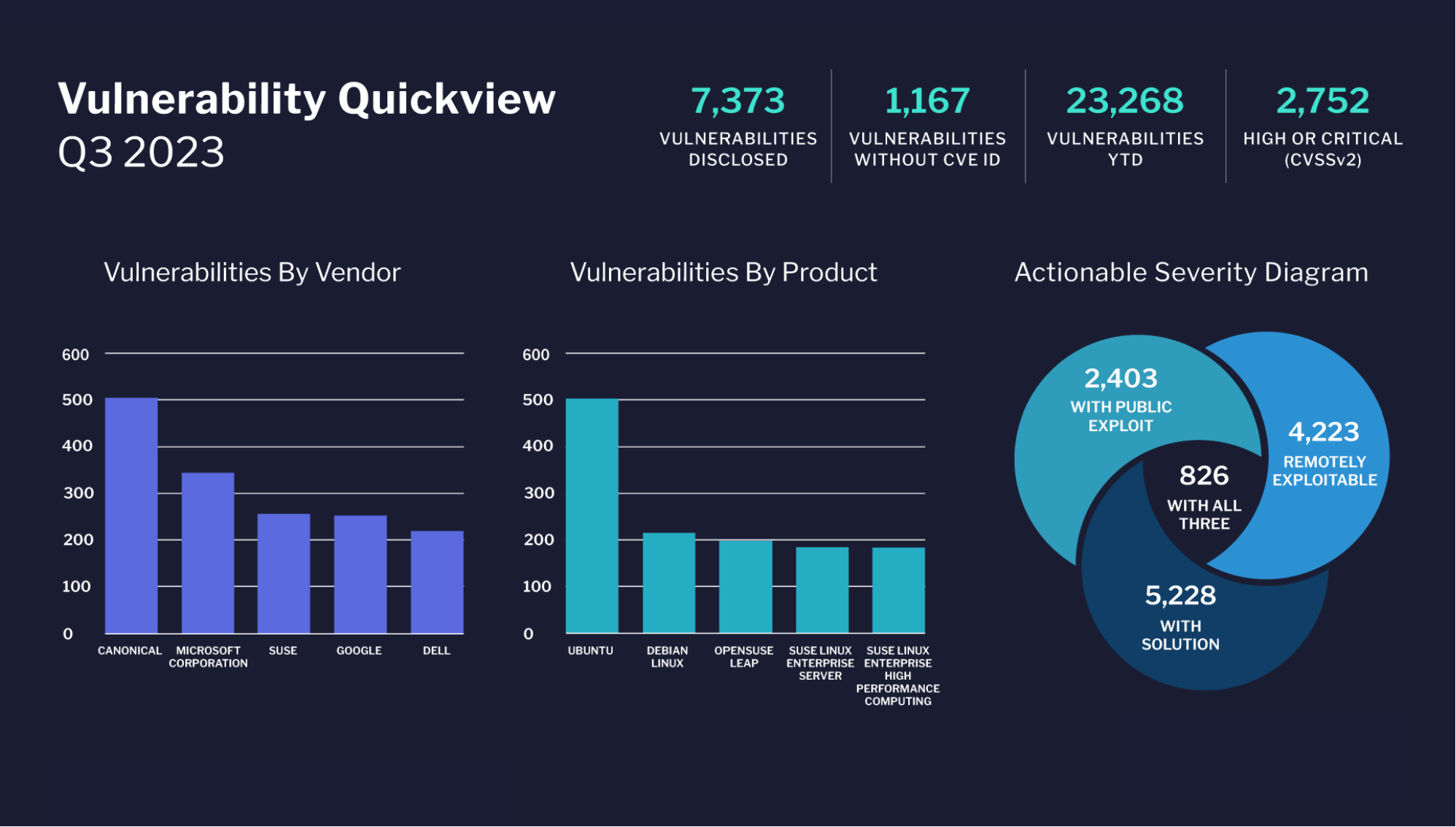
Many cloud providers tout their use of encryption for security, but the term “encryption” can mean many things. Most services use something called encryption-in-transit. To show how this works, we’ll consider a generic cloud-based email service.
As shown in the diagram above, encryption in transit uses encryption to secure a message when it is being transmitted from a phone or computer to a server, often using technologies like SSL (Secure Sockets Layer) or TLS (Transport Layer Security). This prevents an attacker from watching Internet traffic and gleaning the contents of communication. The decrypted message is available at both the device and the server. This makes the server vulnerable to attack, because a successful breach of the server gives the attacker access to all the decrypted messages.
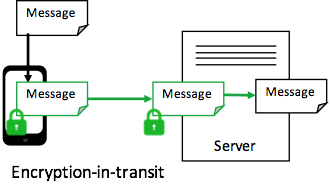
In attempt to address this problem, some cloud services also use encryption-at-rest, as shown below:
Encryption-at-rest means that data is encrypted in the storage media on cloud servers when not being used. Encryption-at-rest could prevent an attacker from accessing information on physical disks that were stolen from a data center — although such physical attacks are exceedingly rare. Encryption at rest still cannot prevent an attack on the server from leaking valuable user data because the server can still “see” the decrypted information. If the server can access the raw data, so can an attacker.
End-to-end encryption can solve the problem by adding the missing link – encryption-in-use – as shown below:
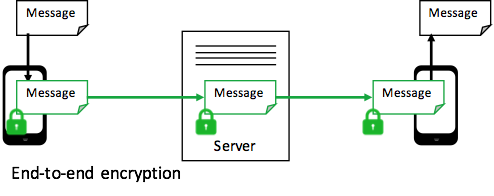
With end-to-end encryption, the server never has access to decrypted data. The message is encrypted in the device of the sender, and it’s not decrypted until it reaches the device of the recipient. Thus, a server attack will not compromise any user information. An attacker may attempt to breach a single user’s device, but such an attack affects only that user – not everyone on the system.
Unfortunately, most major cloud Service Providers do not use end-to-end encryption – including Gmail, Outlook, Dropbox, Yahoo, and many others. This is because these services rely on servers to process emails and files. The servers absolutely must have access to user data.
In conclusion, a different approach to cloud security is needed – one that simply assumes that attackers will breach servers, so everything stored on the server must be encrypted, and decryption only occurs in users’ devices. It’s important that the server never has access to the unencrypted data or the encryption keys to this data. If the server can ever see the unencrypted data, then attackers could see it too. In the end, only a well-designed end-to-end encryption system that assumes the server will be breached can afford stronger protection in the cloud.
By Randy Battat