Roughly 37,000 websites are breached daily. Considering WordPress powers at least 53% of all websites, you can bet a lot of bloggers have to deal with a website hijacking situation. So, don’t leave anything to chance – your blog is only as secure as you make it by following security best practices.
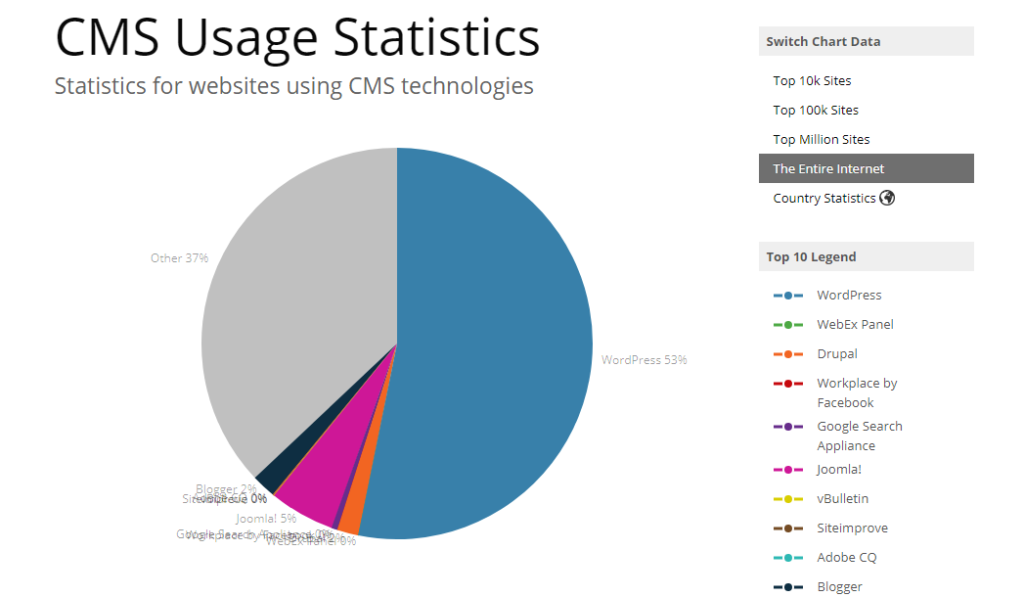
(Source: Builtwith)
We’re launching a 5 part series of articles covering wordpress security in the cloud to educate and have a dialogue about security best practices that are doable, regardless of whether you are a beginner or a seasoned WP blogger.
Without further ado, here are the first steps to establishing a solid foundation to your WordPress security 101.
cybersecurity expert Brian Krebs recently discovered that Equifax’ Argentina website that lets its employees manage credit report disputes from consumers had admin/admin used as its login and password. That, ladies and gentlemen, is how you should NOT manage security.
So, the first thing you should do when setting up your WordPress installation is to change the admin username. Here’s how you can do it:
Tip: you don’t want to display your new admin username to the public. So, click on your new admin name, scroll down to change the nickname and select “Display name publicly as” and select the nickname.
Don’t underestimate the persistence that hackers apply to hijack WordPress blogs. Adding two-factor authentication is just as important as changing your admin username, so, by all means, do that.
The easiest way to enable two-factor authentication in WordPress is through MiniOrange Google Authenticator plug-in. Alternatively, you can use Sucuri, which is a comprehensive solution for WordPress blogs.
To prevent bots from breaching your blog’s security, over-taxing your website, slowing down connections and resulting in denied traffic, you need a captcha solution.
The CAPTCHA WordPress Plugin is one of the easiest ways to enable captcha for registration, login, comment, contact and other forms. This plug-in offers granular controls, so you can white-list people and IPs, as well as choose the type of captcha code.
Spam comments aren’t just annoying; they can bog down your website with excess traffic, or contain malicious links. So, by all means, protect your blog from spam comments. Luckily, Akismet plugin lets you do that for free.
You should always update your WordPress installation to the latest version whenever it’s released. However, you should also hide your blog’s version number from public display because it makes it too easy for hackers to identify which exploits will work best for your WordPress version.
To hide your WordPress version number from public display, you’ll need to backup your blog first. Once you have the current backup:
“add_filter(‘the_generator’,”
This filter will prevent your WordPress blog from displaying its number for everyone to see.
WordPress API is a useful functionality for developers who build custom applications for their blogs. However, it is also a serious security issue because it can be exploited to bypass WordPress authentication system, even the multi-factor authentication.
So, unless you actively deploy custom applications for your blog, you are better off disabling WordPress API. Fortunately, it is as easy as installing Disable REST API plug-in.
By default, WordPress comes with XML-RPC enabled, which allows you to access your blog remotely. The bad news it also opens a possible attack vector, so if you do not intend to publish posts remotely – disable XML-RPC on your blog.
The easiest way to do so without having to modify the code is through the Disable XML-RPC plug-in.
WordPress repository is a treasure trove of free and relatively inexpensive plugins and themes that let you create truly impressive websites without profound technical skills. However, plug-ins are built by people, and people make mistakes. So, a lot of WordPress breaches – 55.9% – are attributed to Vulnerabilities in plugins.
Even though all plug-ins in the WordPress library are vetted, it’s always wise to apply common sense when installing new ones. Here are three tips that should help you choose robust and secure plug-ins:
In the next WordPress security 101 roundup, we’ll discuss the following topics:
Since there’s never any one step to securing the entirety of your WordPress blog, we’ll be covering the essential topics step-by-step. Hope you find these tips helpful!
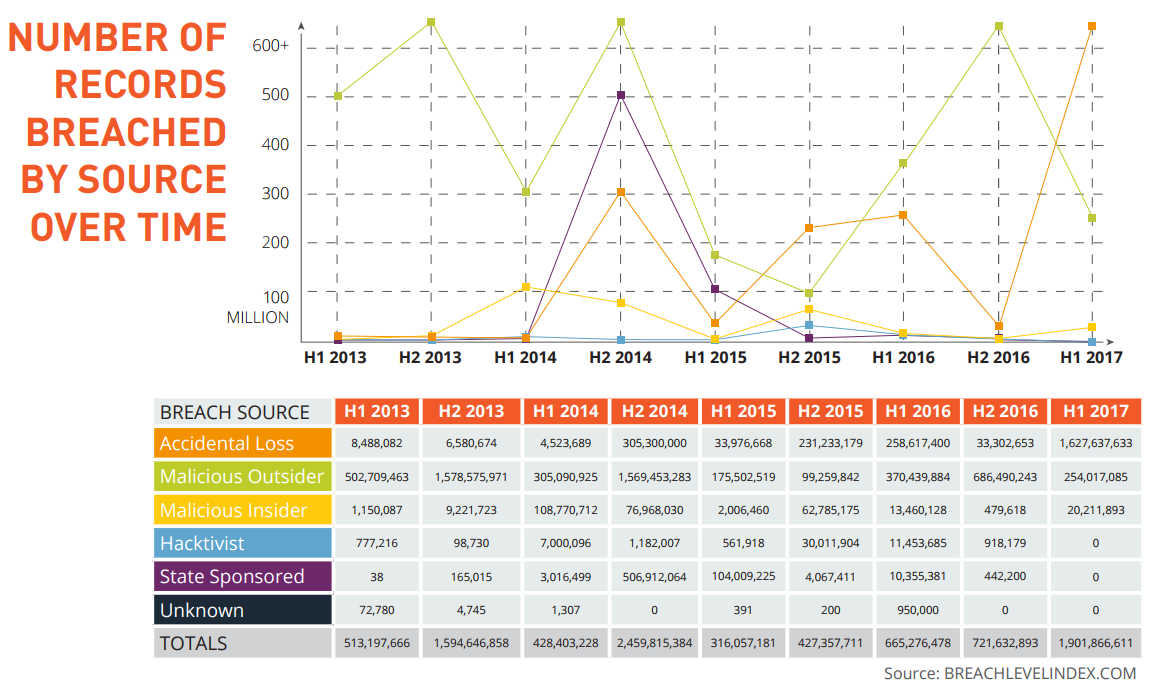
A recent Breach Level Index report by Gemalto, a global cyber security solutions provider, is titled “Poor Internal Security Practices Take A Toll” for a reason. The insider threat is the biggest source of stolen – or lost – records in the first half of 2017, according to the report. Accidental loss accounts for a whopping 86% of all stolen records, with over 1.6 billion records compromised in just six months.
Users prefer convenience over security because it’s in human nature to look for easy ways to get a job done. So, if you want to boost your WordPress security, there is one potential threat that you can’t afford to overlook – yourself and your users.
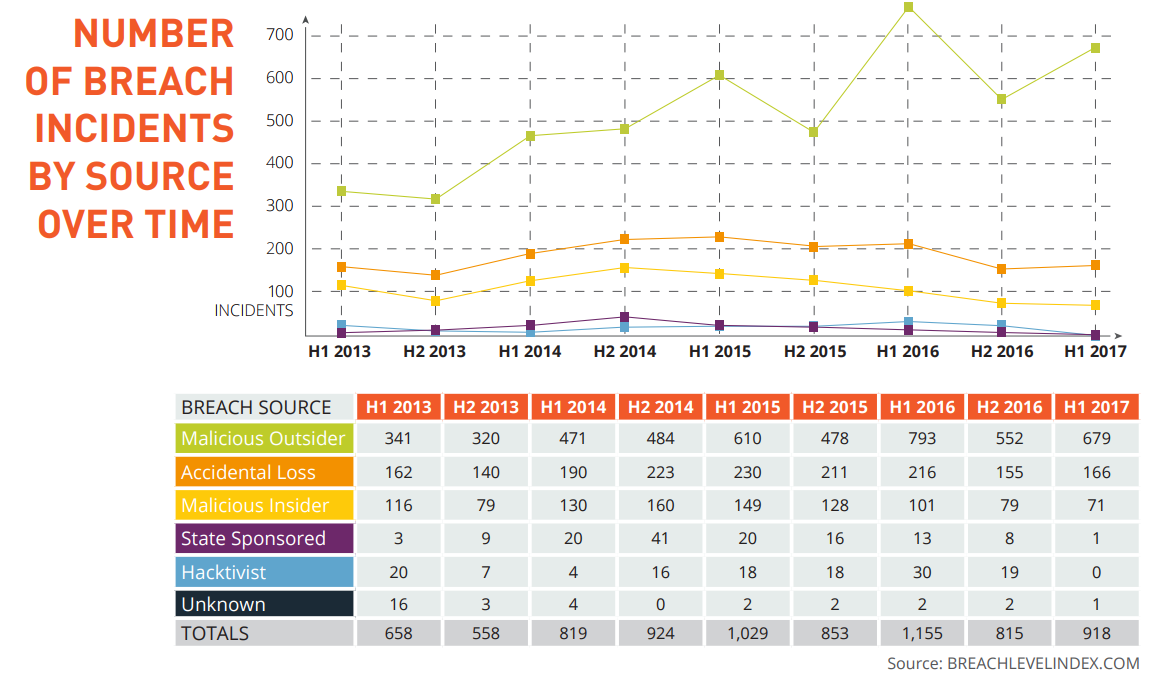
(Infographic Source: Breachlevelindex)
contributors who have access to your WordPress back end can be a part of your defense, or your weakest link (without ever realizing it). Let’s see how you can safeguard your blog against internal threats.
WordPress – and common sense – requires that you use strong passwords, but what is a strong password? A WordPress expert Alex Grant says a strong password is complex and easy-to-memorize at the same time.
Password management programs do a great job of generating and storing your passwords in an orderly manner. This option is feasible if you have multiple blogs since you want to avoid re-using one password across multiple accounts.
Even though automatically generated passwords are secure, they are also impossible to memorize. So, many bloggers just default to weak passwords that are easy to crack.
One simple way of creating strong passwords you can memorize is to use a passphrase based on logic known to you alone, for Instance:
My_goal_is_2_weigh_50_kilo$
The longer the passphrase, the harder it is to crack, and the easier it is to memorize. Use this technique not only for passwords but also for answers to your security questions.
One particular vulnerability that revolves around passwords is you can reset them. If someone gains access to your email, they can reset your WordPress password. If someone can guess – or research – the answers to your security questions, they can reset your password.
So, your password is just a part of the equation, where security of your administrative email account and reasonable complexity of your security answers are equally important.
As of now, WordPress doesn’t offer the functionality to block multiple sign-on attempts. This creates a risk for someone persistent enough to just try different username/password combinations for hours on end. So, you want to limit sign-on attempts to a certain number you deem acceptable.
For blogs with multiple contributors, it’s best if the contributors only have privileges they need to do their work. You need to create the lowest risk environment, where user permissions are restricted to only the necessary minimum.
Otherwise, one user can mess up intentionally or accidentally, and delete someone else’s post, or mishandle their login credentials and expose them.
If a contributor’s account with minimum permissions gets compromised, the malicious party can only mingle with a very limited amount of content on your blog. If malicious actors access the administrative account, you’re in for trouble.
If your contributors use weak passwords, your WordPress backend is vulnerable. Don’t just leave your users to their own devices – set up restrictions that would only allow them to use strong passwords.
The current version of WordPress enforces the use of strong passwords. But if you run an older version, you can add this functionality via the Force Strong Passwords plugin.
One more security vulnerability that comes from users is they forget to log out. When they do, your blog is exposed to great risks. Anyone with access to your contributor’s computer can tamper with your dashboard. So, security best practices suggest that you log out idle users.
That’s it for today! The next WordPress security roundup will focus on:
Stay tuned for more security tips from the WordPress guru Alex Grant.





