In an earlier article we discussed what technology can displace the password.
The proposition of Expanded Password System (EPS) that we advocate is now acknowledged as a ‘Draft Proposal’ for OASIS Open Projects that OASIS has recently launched as a new standardization program. We have publicized an EPS draft specification there.
The EPS is also among the topics to be discussed in Seattle (19-21/September) and Amsterdam (29-31/October) at KuppingerCole’s Consumer Identity World 2018, Besides talking about the EPS as a speaker, the writer will also take part in panel discussions about biometrics and multi-factor authentications.
With these developments as the backdrop, we came up with a motto of ‘Identity Assurance by Our Own Volition and Memory’ for our enterprise. This motto could stand especially well for the emerging concept of ‘Self-Sovereign Identity’.
Passwords need to be remembered and recalled; a password written on a memo is no more than ‘what we possess’, definitely not ‘what we know or remember’, say, not the shared secrets.
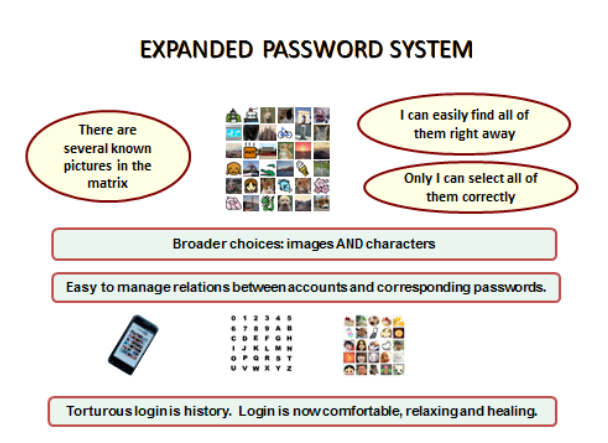
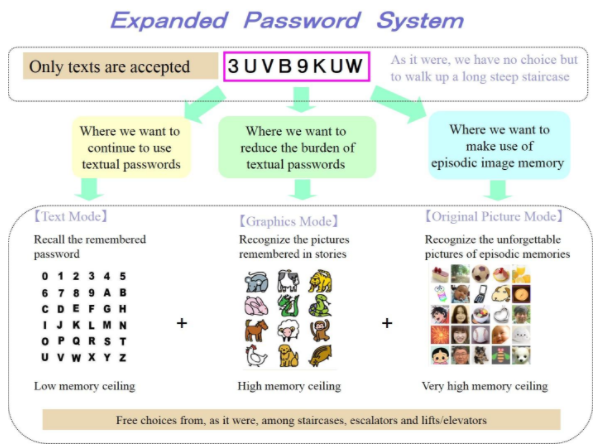
The Expanded Password System that we advocate, which offers a choice of making use of episodic image memory in addition to textual memory, can be viewed as an enhanced successor to text-only password systems on its own. Furthermore, the EPS will enable us to see truly powerful multi-factor authentications with a strong unique password being used as one of the factors for all different accounts, whether indoor or outdoor.
With these developments as the backdrop, we came up with a motto of ‘Identity Assurance by Our Own Volition and Memory’ for our enterprise. This motto could stand especially well for the emerging concept of ‘Self-Sovereign Identity’.
With the EPS used as a rescue-password in case of false rejection, biometric solutions will offer good convenience without sacrificing the confidentiality too much. We would also be able to see truly reliable decentralized ID federations with a strong unique password being used as the master-password for each of single-sign-on services and password management tools. The outcome will be the most highly assured identity achieved through the most reliable “shared secrets”
Identity verification which has been represented by seals and handwritten signatures in the past is not just one of the many factors for information security, but is the very foundation of the social infrastructure without which no social life can exist. This relation between the society and the identity verification will not change so long as humans live social lives. EPS will be a legitimate successor to the time-honored seals and handwritten signatures.
* Feature 1: The idea of using pictures for passwords is not new. It has been around for more than two decades but the simple forms of pictorial passwords were not as useful as had been expected. UNKNOWN pictures that we manage to remember afresh are still easy to forget or get confused, if not as badly as random alphanumeric characters.
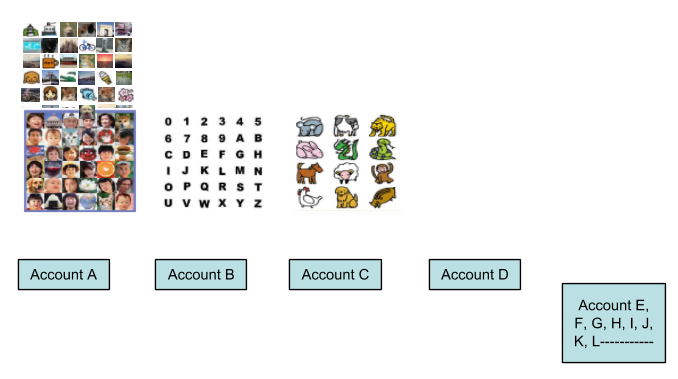
EPS is new in that it offers a choice to make good use of KNOWN images that are associated with our autobiographic/episodic memories. Since these images are the least subject to the interference of memory, it enables us to manage dozens of unique strong passwords without reusing the same password across many accounts or carrying around a memo with passwords on it. Furthermore, we no longer need to manage to remember the relations between accounts and passwords because each account shows its own unique picture matrix.
EPS is inclusive of textual as well as non-textual passwords. Users can retain the textual passwords as before while they expand their password memory to include the non-textual passwords without being impeded by the cognitive effect of “interference of memory”. It is extremely difficult to imagine the users who would suffer disadvantage or inconvenience by adopting EPS..
As for our episodic memory as the cognitive core of our personal identity, you could refer to the following sites.
– Episodic Memories and Your Experiences
https://www.verywellmind.com/what-is-episodic-memory-2795173
– The Cognitive Underpinnings of Continuous Identity
https://www.tandfonline.com/doi/abs/10.1080/15283488.2017.1303384
Feature 2: It is known that episodic memories are easily changeable. What we remember as our experience may have been morphed and not objectively factual. But it would not matter for EPS.
What we subjectively remember as our episodic memory could suffice. From confidentiality’s point of view, it could be even better than objectively factual memories since no clues are given to attackers.
* Feature 3: High-entropy passwords generated from low-entropy passwords
Generally speaking, hard-to-break passwords are hard-to-remember. But it is not the fate of what we remember. It would be easily possible to safely manage many of high-entropy passwords with EPS that handles characters as images.
Each image/character is identified by the image identifier data which can be of any length. Assume that your password is “CBA123” and that the image ‘C’ is identified as X4s&, eI0w, and so on. When you input CBA123, the authentication data that the server receives is not the easy-to-break “CBA123”, but something like “X4s&eIwdoex7RVb%9Ub3mJvk”, which could be automatically altered periodically or at each access if required.
When such high-entropy data are hashed, it would be next to impossible to quickly crack the hashed data back to the original password. Give different sets of identifier data to “CBA123” and the different servers will receive all different high-entropy authentication data. Brute-force attacking of “CBA123” and other similarly silly passwords would perhaps take less than a few seconds with automatic attack programs with clever dictionaries but it could be an exhausting job when criminals have to manually touch/click on the display with their fingers. This function of managing strong passwords by weak text passwords is one of the secondary merits of EPS.
* Feature 4: Passwords & Corresponding Accounts
Being able to recall strong passwords is one thing. Being able to recall the relations between accounts and the corresponding passwords is another. When unique matrices of images are allocated to different accounts with EPS, those unique matrices of images will be telling you what images you should pick up as your passwords.
The Expanded Password System thus frees us from the burden of managing the relations between accounts and the corresponding passwords.
When we deploy a new solution, we often lose something while we gain something else. Does it also apply to Expanded Password System that accepts images as well as characters?
– People who enjoy handling images will gain better security and convenience. The only extra effort required is to get these images registered; but users already do that across social media platforms and seem to love it.
– People who do not love to handle images will be able to opt to keep using characters. They will not lose anything.
– People who use password management tools and single-on-sign services will gain a better security by having a more reliable master password.
– People who use multi-factor authentication for better security will gain an even better security by having a more reliable password as one of the factors.
– People who use biometrics operated together with a fallback password, which provide the level of security lower than the password alone in return for better convenience, will gain a less bad security by having a more reliable fallback password.
– Employers who have to bear the password-reset costs for their employees’ forgotten passwords will see the costs cut back drastically as the employees will now have to ask for the password-reset much less frequently.
– Employees who are held responsible for the damages when criminals grab their passwords will see the much fewer risks as the result of their not using silly passwords, not writing their passwords on paper or not re-using the same passwords across business and personal accounts.
By Hitoshi Kokumai





