As I walked through RSA last week, I was struck by the usual fear laden messages “You’re not safe and never will be but I (vendor) have a silver bullet that will protect you.” And, I wondered if this fear-based approach is deterring a badly needed next generation of cyber security approaches.
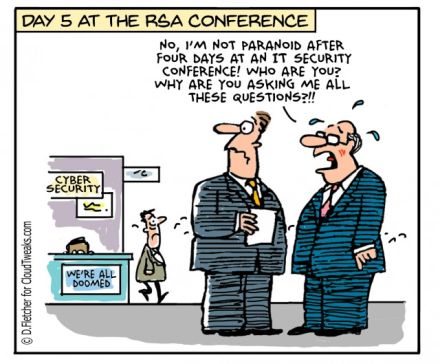
For as long as I have been in the security industry, the focus has been on selling fear and today that fear is firmly anchored around cyber attacks and what could happen when attackers compromise your network and get a hold of your data. As much as the specter of cyber attacks is real the paranoia and hysteria that accompanies it often gets in the way of finding real solutions. While there were some new and innovative technologies on show at RSA this year, many vendors are still touting yesteryear technologies and approaches.
In the Workplace, digitization has changed how we work – it goes beyond the devices we use and where and when we work, and more to the tools and data and our interactions with a expanding networks of people and data. Yet, despite the fear around security breaches, there are few security approaches that truly focus on securing at the data layer with a contextual focus on people and the expanding number of applications in use today.
Digitization increasingly shapes our everyday lives. It’s changed how we manage our personal finances and how we form networks and connect with people socially. Yet despite much media hype around increasing cybercrime, approaches to staying safe online are seem lax compared to the precautions that people might take with their physical safety. For example, parents who would not leave their children unsupervised while outdoors will let young children play on Internet-connected tablet devices, without adequate safety precautions, potentially putting their children at risk at being exposed and in the longer term being exploited online.
By Evelyn de Souza





