The network security market is experiencing a pressing and transformative change, especially around access control and orchestration. Although it has been mature for decades, the network security market had to transform rapidly with the advent of the BYOD trend and emergence of the cloud, which swept enterprises a few years ago. The market persevered, weathering the “end of perimeter security” claims and adapting to become more flexible and dynamic, reaching beyond traditional PCs and servers to new mobile and external endpoints. Those network security vendors that adapted are now poised to take full advantage of the IoT and the billions of connected devices set to revolutionize the enterprise.
Today the IoT is having a similar transformative effect on the enterprise considerably expanded the pool of connected devices that can now be found on a network, with the devices in play no longer limited to the PCs, servers, and smartphones with which IT staff are familiar. They now need to know about air-conditioning units and lighting sensors, fitness bands, and fire alarm panels. Despite the growing proliferation of IoT devices, most enterprises are still trying to discover these new devices. In fact, one of the most difficult issues enterprises now face is visibility; discovering new and unknown devices on their networks, and then establishing those devices’ identities in order to apply the appropriate authentication and access control mechanisms.
Often, most traditional network security appliances are unable to identify new IoT device connections, and visibility into the enterprise networks is, therefore, significantly reduced. This becomes problematic, as unknown devices can easily become attack vectors and raise risk profiles.
To move forward, IT teams need to create new security policies suited to the plethora of IoT connected devices, and perhaps employ new tools to fit them into enterprise networks in a way that adheres to internal requirements. The Target breach is an excellent, if unfortunate, case study of what can happen when IoT endpoints are not properly controlled.
A number of companies are making headway in adapting traditional network security to the IoT, including Bastille, ForeScout, Cisco, Fortinet, F5 among many others.
Identification and localization of specific nodes will become a fundamental issue with the billions of IoT devices envisioned to appear in the near future. Security vendors that are able to help enterprises overcome the obstacle of discovering new and unknown devices on their networks will also need to figure out how they can provide security features or, at the very least, integrate with those appliances that can.
Beyond that, authentication and access control will become critical. Certification can provide a level of authentication and access control for IoT nodes. Alternatively, authentication mechanisms for the perception and network layers can prevent impersonation attacks. A PKI can help to achieve strong two-way authentication. Access control technology can be correctly implemented simply so that certification technology is able to ensure identification. Various authentication protocols can be employed, such as hash-lock, hash-chain, distributed RFID inquiry—response authentication, LCAP, clap agreement, re-encryption mechanism, etc. The use of such protocols will depend, for example, on the suitability of the various RFID applications and the desired level of security.
At the network level, various mechanisms can be used, including end-to-end authentication, key negotiation, key management or even intrusion detection mechanisms. Various distribution protocols are enabled through key management that can be applied to the IoT, including simple key distribution, key pre-distribution agreement, dynamic key management protocol, and hierarchical key management protocol.
Intrusion detection and prevention is not widespread for sensor networks in IoT. In fact, due to the complexity of many of these networks and the relatively low computation resources available, traditional IDS/IPS systems are simply not effective in these scenarios. However, next-generation research presages just such technologies adapted for the IoT. Methods have been proposed to develop a system of intrusion detection according to the past access frequency of a Thing’s label or for various time-based models (PDR, P2DR, P2DR2, etc.). Another novel approach seeks to simulate real-time defense of IoT environments by studying artificial immune system concepts that imitates the mechanisms of a biological immune system.
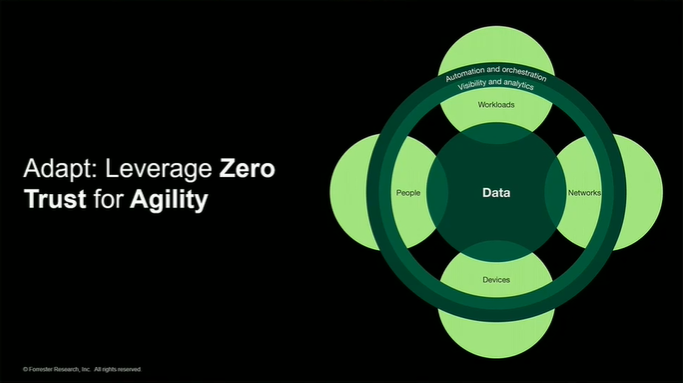
Security and safety in the IoT essentially boils down to establishing trust: in the integrity of the applications, in the security of the networks, in the confidentiality of the data, and in the safety of the devices. The IoT is a complex space, and any tool that can simplify management and control of IoT devices will be highly valuable.
By Michela Menting