It wouldn’t be wrong to say that voice biometrics is the way of the future, when it comes to verifying the identity of customers contacting call centers. Market research firm Forrester, for one, predicts it will be the go-to authentication solution for financial institutions by 2020.
But it is just as accurate to say that voice biometrics is rapidly being recognized as today’s best practice as well. Already, major businesses in such sectors as banking and finance, healthcare, telecom, and other security-sensitive fields are recognizing that voice authentication offers a wide array of compelling benefits.
For one thing, it vastly improves the customer experience, by doing away with the unwelcome interrogations that call centers traditionally needed to go through to identify each caller. Since voice authentication relies on the caller’s normal conversation itself, and verifies a caller’s identity in real time without requiring any effort on the caller’s part, the process is frustration-free, unlike a barrage of questions. In fact, most consumers say they prefer voice authentication to jumping through the current hoops. Secondly, because voice authentication takes into account more than 100 variables of speech in a sophisticated mathematical expression, it offers a high degree of accuracy and security that rivals or exceeds the certainty of the fingerprint.
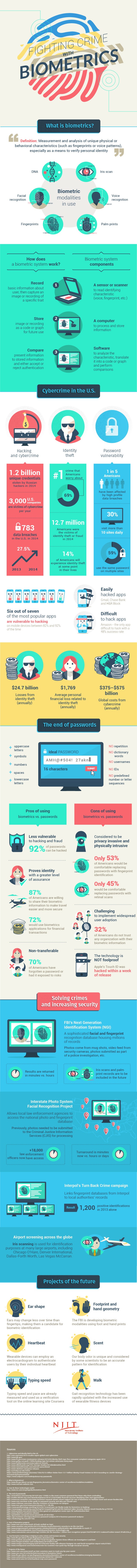
(Infographic Source: NJIT)
And, in no small matter for businesses, it offers benefits that go directly to the bottom line. By eliminating time spent on verifying identity every time the phone rings, it frees up employees for the revenue-generating activities at the heart of their jobs.
That said, it is still the case that making the transition from the old way to the new and improved way doesn’t come without challenges. Fortunately, with the right guidance for efficient implementation, these adoption challenges become negligible.
Everybody wins with voice biometrics. It puts the customer first, because it eliminates extra steps and frustration. Businesses and customers alike benefit from the added security it provides, and from the shorter call times, which pay off in convenience for the customer and increased ROI for the company – especially when the company has selected a biometrics solution that adapts to all necessary integrations.
By Naomi Webb