The Dangers of Facial Recognition Technology
Facial recognition technology has become increasingly prevalent in our daily lives, from unlocking our phones to boarding airplanes. While this technology may seem convenient, its implications go far beyond mere convenience. There are real dangers associated with facial recognition technology that have caught the attention of policymakers, privacy advocates, and civil rights groups alike.
The potential for abuse by law enforcement is one of the most concerning aspects of facial recognition technology, as highlighted in a recent BBC article reporting that Clearview, a facial recognition firm, has conducted nearly a million searches for US police, according to its founder.
But it’s not just law enforcement that poses a threat. Private companies are also collecting massive amounts of facial data, often without the knowledge or consent of the individuals being surveyed. As privacy activist Edward Snowden has noted, “facial recognition is the most perfect tool of oppression ever created.” Once someone’s face is in a database, it can be used to track their movements, monitor their activities, and even discriminate against them based on their appearance.
The dangers of facial recognition technology are clear, and the need for regulation is urgent. As we continue to embrace new technologies, it’s important that we do so with our eyes open and with a full understanding of the potential risks.
“Facial recognition technology has the potential to be a game-changer in law enforcement and security, but it is not without its risks. The technology is prone to errors, bias, and abuse, and can have a chilling effect on freedom of expression and assembly. It is important that we strike the right balance between security and privacy, and put in place strong safeguards to prevent abuses.” – Vera Jourova, Vice President of the European Commission for Values and Transparency.
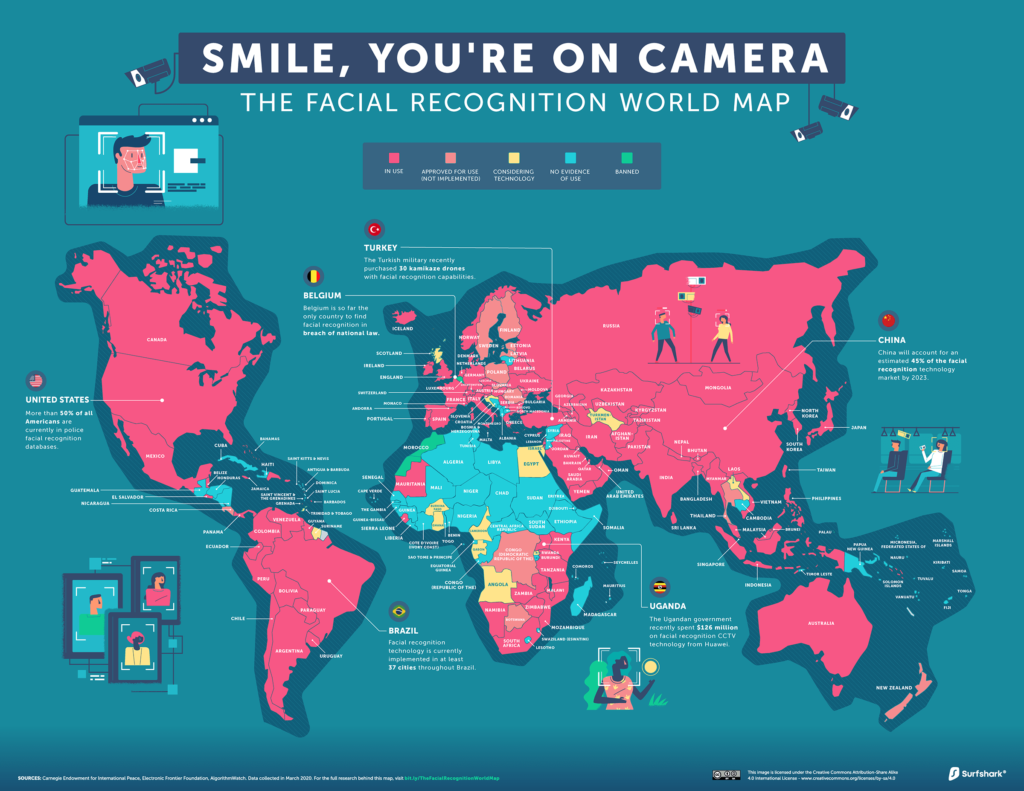
https://surfshark.com/facial-recognition-map
Facial recognition technology (FRT) is a type of technology that uses algorithms and artificial intelligence to analyze and identify individuals based on their facial features. While FRT can be useful in some contexts, such as law enforcement or security, it also poses a number of dangers and concerns.
- Invasion of privacy: One of the main concerns with FRT is the invasion of privacy. With this technology, individuals can be identified and tracked without their knowledge or consent, even in public spaces.
- Bias and discrimination: Another issue with FRT is the potential for bias and discrimination. Many FRT systems have been found to be less accurate when identifying people of color, women, and other marginalized groups. This can lead to unfair treatment and discrimination.
- False positives: FRT can also produce false positives, which can result in innocent people being accused or targeted. This can have serious consequences, particularly in the context of law enforcement.
- Security risks: FRT systems can also be vulnerable to hacking and data breaches, which could expose sensitive information and compromise the security of individuals and organizations.
- Lack of regulation: Finally, there is currently a lack of regulation around FRT, which means that there are few safeguards in place to protect individuals from its potential dangers.
“Facial recognition is a powerful technology that can be used for good or bad purposes. But without proper regulation and oversight, it can lead to abuses of power, invasions of privacy, and violations of human rights. It is important that we have a serious discussion about how to regulate and use facial recognition technology in a responsible way.” – Tim Cook, CEO of Apple
A few of the main vendors operating in this area are:
- AnyVision is an AI-powered facial recognition and video analytics platform used in a variety of industries, including security and surveillance, retail, and transportation. Its technology is designed to be accurate, scalable, and secure, with features such as facial recognition, object detection, and behavior analysis. AnyVision’s platform is also flexible and can be integrated into existing security systems and cameras. https://www.anyvision.co/
- Face++ is a facial recognition technology company based in China. They offer a variety of solutions including face recognition, face analysis, and face search. Their technology is used in a variety of industries including finance, security, and retail. https://www.faceplusplus.com/
- Megvii is a technology company specializing in facial recognition software. Its AI-powered face recognition technology can be used in a variety of applications, including security and surveillance, retail, banking, and public services. Megvii’s technology is designed to be accurate, fast, and scalable, with features such as age and gender detection, emotion analysis, and real-time tracking. https://en.megvii.com/technologies/face_recognition/
- Clear is a secure identity verification company that provides expedited access to venues and services such as airports, stadiums, and other events. It uses biometric data such as fingerprints and facial recognition to verify a user’s identity, allowing them to bypass traditional security checkpoints. Clear also offers a health pass feature, allowing users to securely store and share their COVID-19 vaccination status and test results. https://www.clearme.com
- NEC Corporation is a technology company that offers a range of solutions including facial recognition technology. Their technology is used for various applications such as law enforcement, border control, and access control. NEC’s facial recognition technology is known for its accuracy and speed. https://www.nec.com/en/global/solutions/safety/face_recognition/index.html
- Microsoft is a global technology company that offers a range of solutions including facial recognition technology. Their facial recognition technology is part of their Azure Cognitive Services offering and is used for various applications such as security, access control, and customer engagement. Microsoft’s facial recognition technology is known for its accuracy and ability to work with low-quality images. https://azure.microsoft.com/en-us/services/cognitive-services/face/
- Clearview AI is a technology company that offers facial recognition software to law enforcement agencies and private companies. The software uses a proprietary algorithm that can match faces in real-time against a database of over 3 billion images. However, the company has faced controversy over its methods of data collection and privacy concerns. https://www.clearview.ai/
- Clarifai is a company that provides AI-powered image and video recognition technology, including face detection. Their AI face detection technology is designed to detect faces in images and videos with high accuracy, even in challenging conditions such as low lighting or occlusions. The technology can be used in a variety of applications, including security and surveillance, social media, and e-commerce. Clarifai offers an API that developers can use to integrate their face detection technology into their applications. https://www.clarifai.com/models/ai-face-detection
- Trueface is a facial recognition technology company that provides AI-powered facial recognition, age and gender detection, and emotion analysis. Its technology can be used in a variety of industries, including security and surveillance, retail, and healthcare. Trueface’s technology is designed to be accurate, fast, and scalable, with features such as real-time tracking and analytics. The company also prioritizes privacy and security, with features such as data encryption and on-premise deployment options. https://www.trueface.ai/
- IBM is a global technology company that offers a range of solutions including facial recognition technology. Their facial recognition technology is part of their Watson Visual Recognition offering and is used for various applications such as security, access control, and customer engagement. IBM’s facial recognition technology is known for its ability to work with large datasets and its accuracy. https://www.ibm.com/watson/services/visual-recognition/
There are a few ways to protect yourself from facial recognition software:
- Avoid posting photos online: Be careful about the photos you post online, as they can be used to create a facial recognition profile.
- Use privacy settings: Adjust your privacy settings on social media to limit who can see your photos and profile information.
- Use strong passwords: Use strong passwords for your online accounts to prevent unauthorized access.
- Opt out of facial recognition databases: Opt out of facial recognition databases where possible, such as the ones used by law enforcement.
- Use anti-facial recognition tools: There are also tools and apps available that can disrupt or block facial recognition technology, such as face masks, anti-facial recognition glasses, and privacy-focused browsers and search engines.
It’s important to note that while these methods can help protect your privacy to some extent, they are not foolproof and may not always be effective against advanced facial recognition technology.
Overall, while FRT can have some useful applications, it is important to be aware of its potential dangers and to advocate for responsible and ethical use of this technology.
By Gary Bernstein





