Recently, the US Justice Department has told a federal magistrate judge that two government agencies are investigating allegations of misconduct during the Thomas Drake – National Security Agency (NSA) leak investigation in 2010. They are the Office of Special Counsel, a federal agency that is responsible for investigating complaints by whistleblowers, and a Justice Department committee that investigates allegations of malpractice by offices of inspectors general.
Drake was indicted on April 14, 2010 for the willful retention of classified national defense information; obstruction of justice; and for making a false statement. A former employee of the NSA who “held a Top Secret security clearance,” Drake accepted a plea deal from the Obama government just days prior to the start of his espionage trial in June 2011. Instead of facing a total of 10 counts of felony and the possibility of 35 years in jail, he was required to plead guilty to what was described as “a mere misdemeanor.” In terms of the plea bargain, no fines or jail time would be imposed on him.
The new investigation launched this year is a result of accusations by Drake that the Pentagon’s inspector general’s office might have destroyed possible evidence in the form of secret documents. These accusations were made in April, and US magistrate judge Stephanie Gallagher was appointed to evaluate them. On May 13 she asked the Department of Justice to investigate further and make recommendations in terms of whether or not to take legal action.
In written correspondence last week, dated June 11, the chief of the Justice Department’s Public Integrity Section, Raymond Hulser confirmed that the inquiry was “ongoing,” and being handled by the Office of Special Counsel (OSC). He also stated that if the OSC found “evidence of criminal conduct,” it would refer the evidence to the Justice Department for “appropriate action.”
The destruction of any form of evidence that might be used in a criminal court case could violate the evidence retention rules that federal agents and prosecutors are expected to follow. However, it is not known what possible action Gallagher could order if it was found that evidence held in the Pentagon inspector general’s office had in fact been destroyed.
Drake is currently being represented by Jesselyn Radack, national security director of a whistleblower advocacy group, the Government Accountability Project, who also represented Edward Snowden. She strongly believes that the documents were destroyed “outside of normal policy,” but has not gone so far as to accuse the Pentagon or prosecutors of misconduct.
Radack was not part of the original criminal defense team that represented Drake during 2010 and 2011, and she has said that she found out about the alleged destruction of records relating to Drake’s case via the OSC. The information she has comes from secret complaints that were filed by officials from the Pentagon inspector general’s office, some of whom still work there. It is not known who they are as they formally requested the OSC respect their anonymity for fear of retaliation.
It is understood that the Justice Department claimed prior to Drake’s impending 2011 trial that some documents had been destroyed, but that this has been done according to “a standard document destruction policy.” Radack maintains that there is no such policy, and that rather the inspector general’s office has a Records Management Program that demands documents are kept on file.
Drake has been quoted as saying these allegations are his last chance to hold the NSA accountable for “illegal retaliation” against whistleblowers.
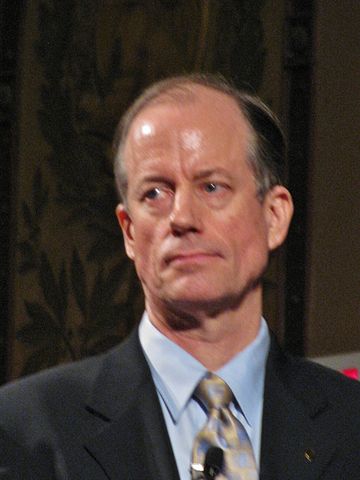
(Image Source: Thomas Drake / Wikipedia)
By Penny Swift





