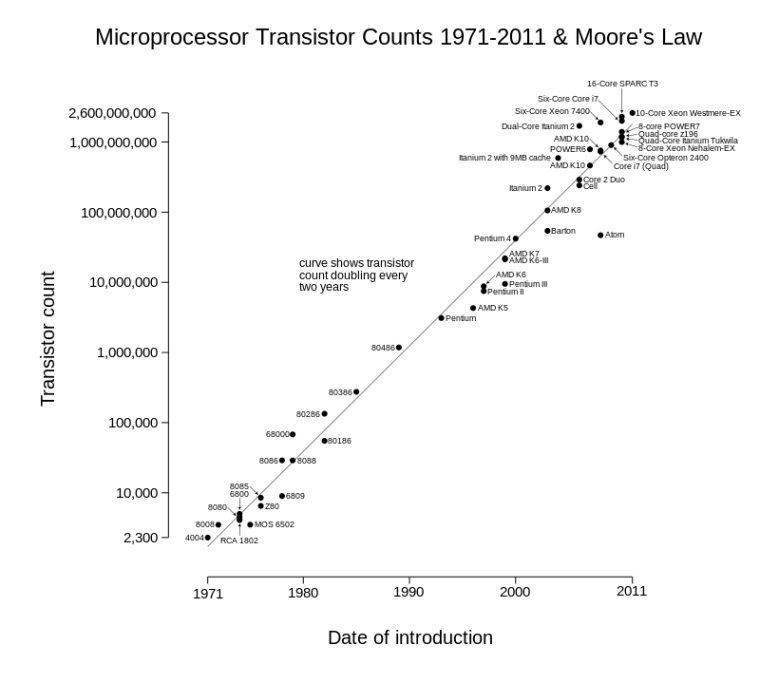
It is not possible to stare with absolute clarity into the future. None of us has a crystal ball. But there is certainty in knowing that the path to progress on which our future lies curves steeply upwards. Gordon Moore originated a concept, now called Moore’s Law, in 1965. It was intended to describe the constant doubling of processing power in semiconductor chips every two years in an exponential fashion. Although this law was originally designed to describe the progress of computer components, it has subsequently been adapted by numerous futurists to reflect the pace of human technological change in general.
Technologies such as the cloud, mobile devices, and the Internet of Things have not only increased collective processing power, but have also distributed it worldwide so that human beings from every corner of the planet can access and use the technologies. This is good news when efforts are applied to innovation and progress, but not so good news in terms of threats to network security.
Following the upward progression of Moore’s Law, security specialists face an ever-increasing variety and sophistication of attack vectors, happening 24 hours a day and mutating constantly. It becomes increasingly difficult to guard a castle when the attackers are so numerous, agile and versatile, but such is the life of the cloud security professional.
For many organizations, IT-related security professionals play a game of cat and mouse with attackers, and this is usually performed in reactive, firefighting mode. At a senior management level, a lack of true understanding of the severity and frequency of attacks, combined with perpetual concerns over costs, have left many organizations understaffed in this area. The problem with this scenario, much like it is in any war, is that strategies cannot be deployed without a higher level vision and a long-range plan. Security specialists who exist purely in firefighting mode represent common foot soldiers, marching or running toward battle but with little overarching strategy of how to outflank the enemies in a more decisive fashion.
Cloud security is a profession that, possibly more than most, cries out for effective time management. Deficiency in this skill is generally not because of any ignorance of its importance, but simply a result of the workload at hand. Most security specialists readily state that given their choice they would prefer to invest a portion of their working time to research, education, and preparedness planning. This, they feel, would lead to far more effective security protocols, both in terms of technological barriers and also in teaching employees the correct techniques and habits for safe computing, password management and general network security hygiene.
Assignment of time in this fashion is an ideal implementation of the Pareto principle, otherwise known as the 80/20 rule, in this case, pointing to the fact that more could be achieved by dividing the workload into two camps: planning and preparedness (20%), and then action and deployment (80%). Only by allowing time for research, review and strategy, can a security professional and the employer gain the upper hand in the constant battle with cloud-based enemies.
A simple example of the strategic clarity that the 80/20 principle can deliver is the Friday effect. Network security company Cyren pointed out recently that Fridays are the most dangerous days for the delivery of Malware.
This is predicated on the fact that employees prefer to take their devices home with them for the weekend, and consequently turn to less-than-secure Wi-Fi connections for doing work and returning emails. When employees work outside a secure firewall, cyber criminals can exploit this weakness, leading people to unwittingly download malware, which is then reinserted into a company’s network upon their return to work on Monday. This type of strategy, which may appear fiendishly straightforward, has a pattern that can best be perceived through a higher level view, and is not available to be picked up by security specialists already overwhelmed by immediate crises.
As companies invest in cloud security, they should be seeking certified professionals, such as the Certified Cloud Security Professional (CCSP℠) from (ISC)2®, a global leader in information, cyber, software and infrastructure security certifications, who have the demonstrated experience, knowledge and skills to competently address the many challenges of this role – from reacting to threats to ongoing maintenance of secure cloud infrastructure to communicating effectively with business leaders. This is a lot to ask of any individual and, similarly, it is a lot to ask of a company: allowing time for the expert to prepare for the future while battling the present. It requires resources, and senior-level commitment.
The one constant, however, is that this will not change. In fact, it will only increase. A certified cloud security professional is there to establish and maintain appropriate defenses so organizations can benefit from the full power of cloud computing to grow their business.
For more on the CCSP certification from (ISC)2 please visit their website. Sponsored by (ISC)2.
By Steve Prentice





