With data security breaches and identity thefts increasing every year, it is important for businesses to consider the impact this might have on their customers and reputation. Luckily, there are a lot of options that make protecting your data easy, and much more affordable than cleaning up a security breach.
As the CEO of a medium-sized company, I understand that data security is an integral part of running any business. Taking the time to ensure all your data is secure, with an effective backup plan in case a security breach happens, can be a complicated task, and many small businesses may not have the knowledge or tools to implement their own security solutions. There are a couple ways to approach this daunting task.
One solution is adding the necessary resources to manage and house your data internally. Initially, this sounds like the easiest option – especially if you like that idea of saving and managing data in-house. However, this solution might become a problem if the expertise or resources are not there. Another solution is to let a third party handle the security work for you. It may seem risky to trust a third party with your data, but finding a third party that you trust can provide some great benefits that cannot be easily accomplished in-house.
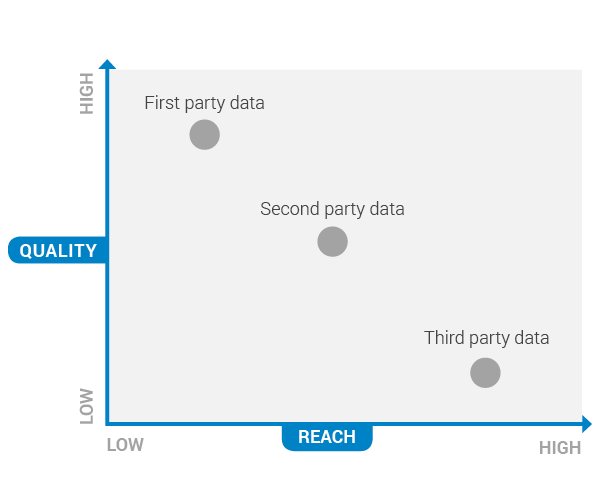
(Image Source: Datacratic)
Here are some important factors to consider if you’re unsure about having someone else secure your data:
Trust is the most important factor when outsourcing any service, but it’s especially important when it comes to your data. When selecting a third party service provider, ask around, and gauge their reputation. Asking for references, as well as doing your own research would be a good start. If you’re going to trust this company, you should see what others who have already done so have to say. Take a look at a few different companies to give yourself an idea of how reliable they are, compared to each other. Ultimately, reputation should play a big role in your decision. If they have a great reputation, it’s probably safe to say they are a good candidate. Service Providers with a poor reputation will not be able to stay in the data management business for very long.
When choosing a third party to handle your data, it’s important to see how their solution will be implemented and customized to fit your specific business needs. We recommend making sure the company you choose takes the time to assess your business model and network, but also develops a plan that fits with your infrastructure. This critical factor can benefit your business in both how your third party works for you, and how secure the data will be. At the end of the day, you can reap the benefits as if you had an internal team, without the resource allocation.
How will your data be handled and stored? How does it differ from what you could implement in-house? How will your third party respond if something happens to your data? These are all important things to consider when finding an outsourced resource for data backup. Going back to plan customization, try to look for a company that has more than one contingency plan available to implement. A good safeguard would be having more than one backup plan in place. Housing your data within the cloud is another important factor to keep in mind. Storing data exclusively in solid hardware is not ideal – if your hardware is damaged, your data could be as well. Cloud solutions also provides the benefit of being stored across multiple locations.
As mentioned, the key signal when choosing an outsourced data-management provider is trust. Do you feel they would be a simple outsourced resource, or a partner — an integral asset to your internal team? What kind of comprehensive data security, recovery, and backup plans do they offer? Ensure that the plan they offer covers not only the security of your data, but also what happens if there is a breach, and how they can get you back on track. It’s important to note that while many small to medium-sized businesses can enact a successful data plan, these third-party sources are in the business of data storage and security; it’s not just their passion and expertise, it’s also their lifeblood. Confidence in who’s managing your data will help alleviate concerns and allow you to focus on what’s important: running your business.
By Matthew Cleaver