Cyber Threat Intelligence
In an era of rapid digital transformation, we have witnessed a concerning evolution in the cyber threat landscape. Recent data analyses, as illustrated in the “Cyber Threat Intelligence Index: Q3 2023” report, underscore the escalating complexity and prevalence of cyber vulnerabilities and malware types.
The dominance of malware families like CobaltStrike and SmokeLoader, combined with the extensive use of tactics such as Command and Control and Defense Evasion, indicates a sophisticated and stealthy approach by cyber adversaries. Furthermore, the sharp increase in the number of vulnerabilities, especially those that are publicly exploitable or without a known solution, paints a grim picture for cyber defenders.
As we step into 2024, there’s a palpable apprehension surrounding the realm of cyber threats. The interconnected nature of today’s world, bolstered by the Internet of Things (IoT) and extensive digital integration, has broadened the attack surface for malicious actors. It’s not just large corporations or governments that are at risk; everyday users, small businesses, and vital infrastructure components have found themselves in the crosshairs of these cyber onslaughts. The tangible effects of such attacks can range from financial losses and data breaches to the crippling of essential services and the erosion of public trust in digital systems.
The statistics from the third quarter of 2023 serve as a stark reminder that complacency is no longer an option. The shifting dynamics of malware types, with Trojans and Remote Access Trojans leading the charge, highlight the importance of proactive defense and staying ahead of the threat curve. As ransomware, though constituting a smaller percentage, continues to wreak havoc with its high-impact attacks, the urgency to prioritize cybersecurity has never been clearer.
The growing fear of cyber-attacks are not just based on numbers but on the evolving sophistication, scale, and potential ramifications of these threats. Now, more than ever, there’s a collective call to action for individuals, businesses, and governments alike to fortify their cyber defenses, invest in research and training, and foster collaboration to counter these looming digital dangers.
Vulnerability Quickview
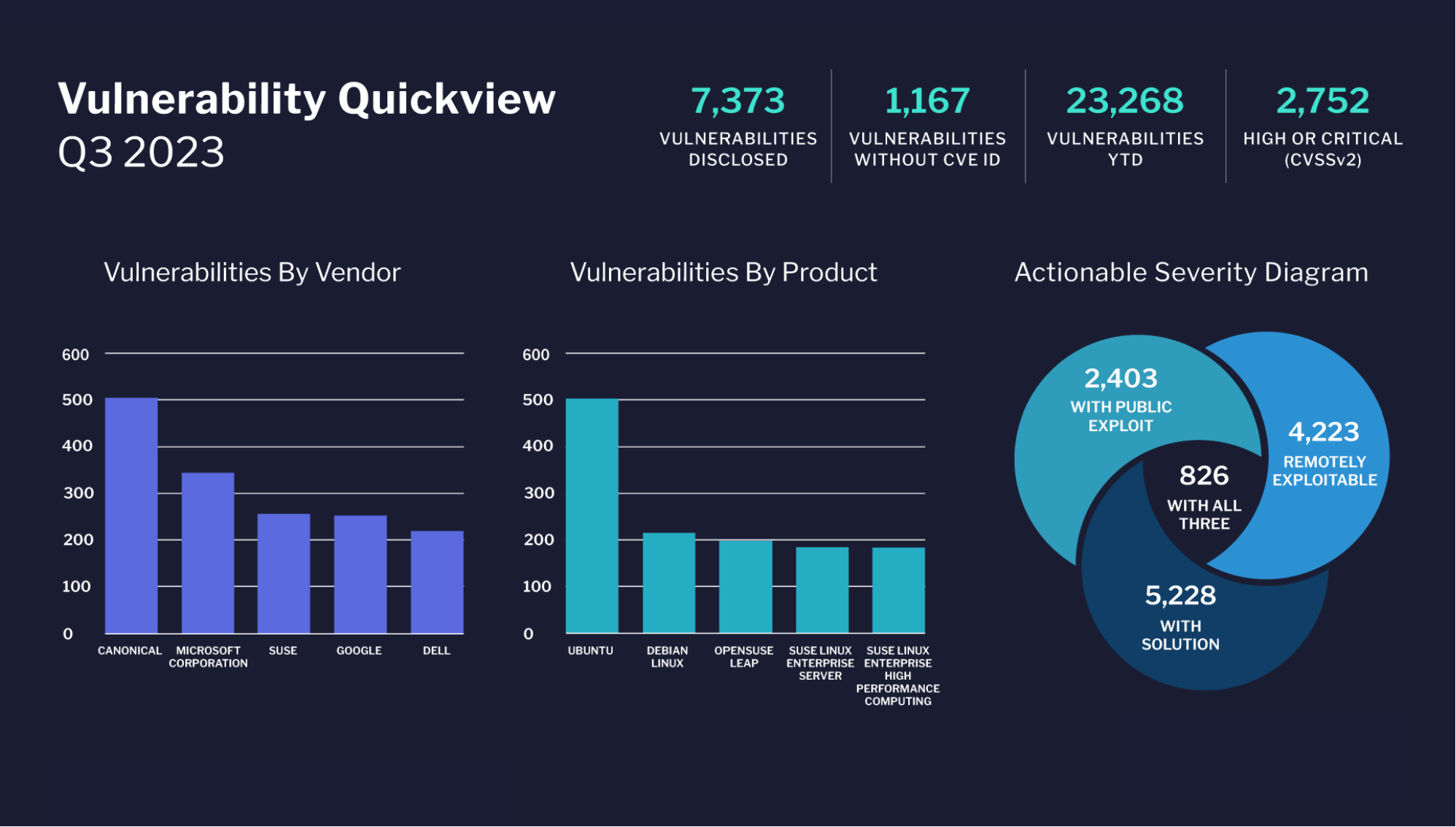
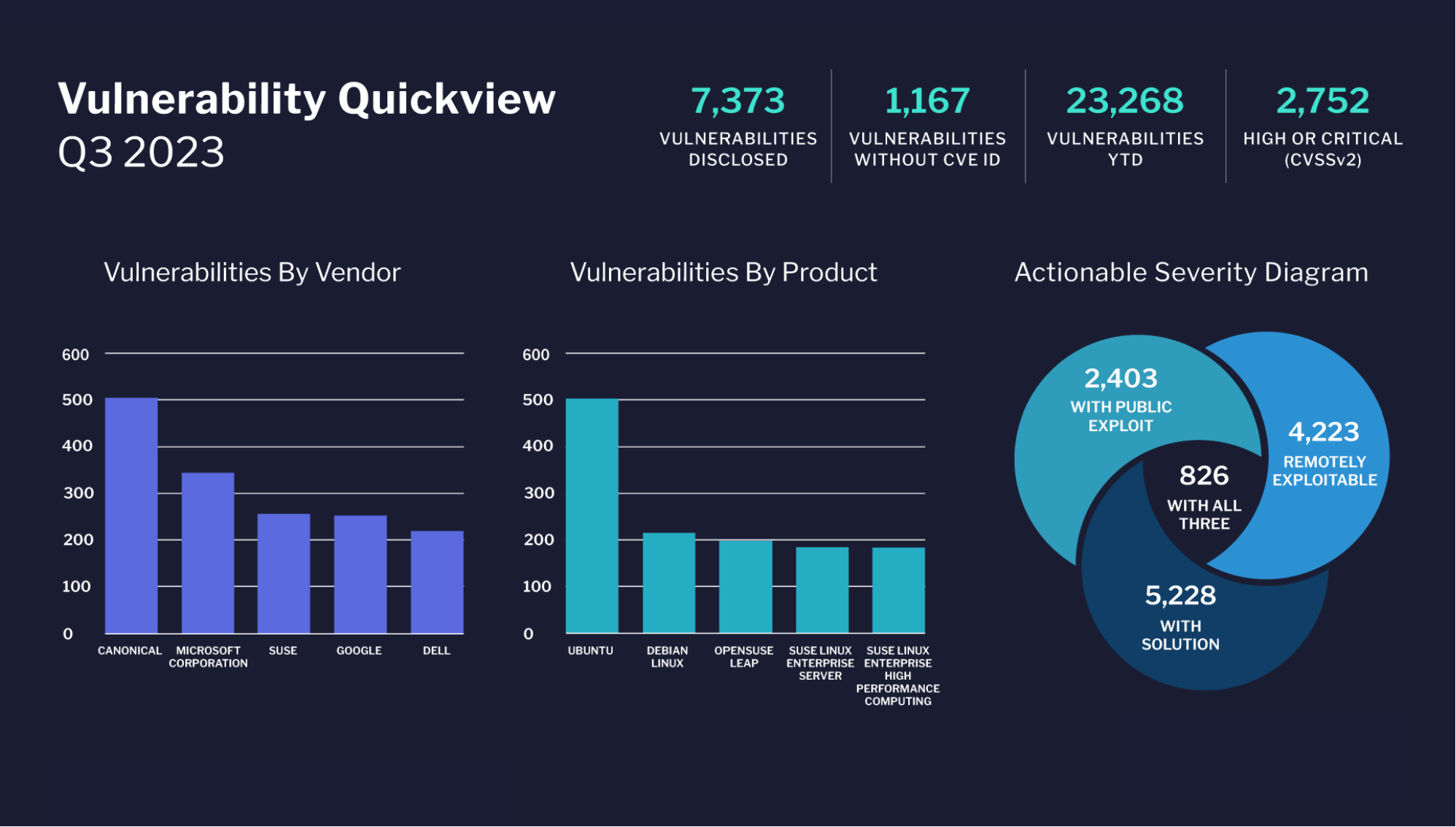
The graphic provides a comprehensive overview of the vulnerability landscape for the third quarter of 2023, breaking down vulnerabilities by vendor and product, as well as presenting a severity diagram that highlights vulnerabilities based on exploitability and the availability of solutions.
(Image source: https://flashpoint.io/blog/cyber-threat-intelligence-index-q3-2023/)
Overall Vulnerability Statistics for Q3 2023:
- 7,373 vulnerabilities have been disclosed.
- 1,167 vulnerabilities have been disclosed without a CVE ID.
- Year-to-date (YTD), there have been 23,268 vulnerabilities.
- 2,752 of these vulnerabilities are categorized as high or critical, based on the CVSSv2 rating system.
Vulnerabilities by Vendor:
- Canonical leads with close to 500 vulnerabilities.
- Microsoft Corporation follows with just over 400 vulnerabilities.
- SUSE has slightly fewer than 400 vulnerabilities.
- Google and Dell have fewer than 300 vulnerabilities, with Dell having the least among the listed vendors.
Vulnerabilities by Product:
- Ubuntu has the highest number of vulnerabilities, close to 500.
- Debian Linux stands next with a little over 400 vulnerabilities.
- Products like OpenSUSE Leap, SUSE Linux Enterprise Server, and SUSE Linux Enterprise High Performance Computing each have vulnerabilities numbering between 100 and 300, with OpenSUSE Leap showing the highest among the three.
Actionable Severity Diagram:
- 2,403 vulnerabilities come with a public exploit.
- 4,223 vulnerabilities are remotely exploitable.
- 5,228 vulnerabilities have a solution available.
- A subset of 826 vulnerabilities are unique in that they possess all three attributes: they have a public exploit, are remotely exploitable, and have a solution available.
Malware IOCs Quickview
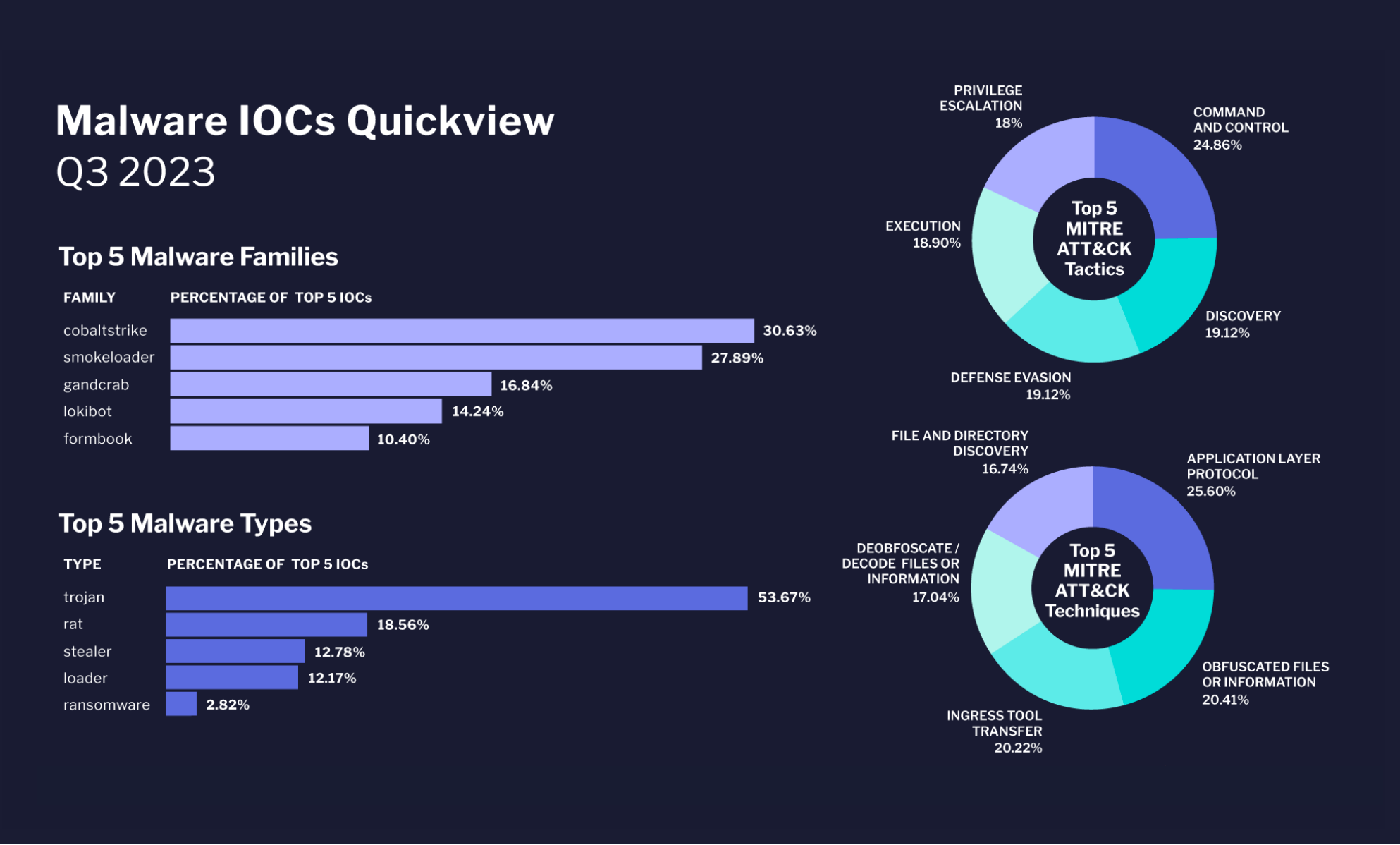
This graphic offers a detailed view of the malware landscape for the third quarter of 2023. It outlines the dominant malware families and types, and also breaks down prevalent cyber-attack tactics and techniques according to the MITRE ATT&CK framework. The data emphasizes the ongoing threat of CobaltStrike as a malware family, the continuous prominence of Trojans, and the significant use of command and control tactics by cyber adversaries.
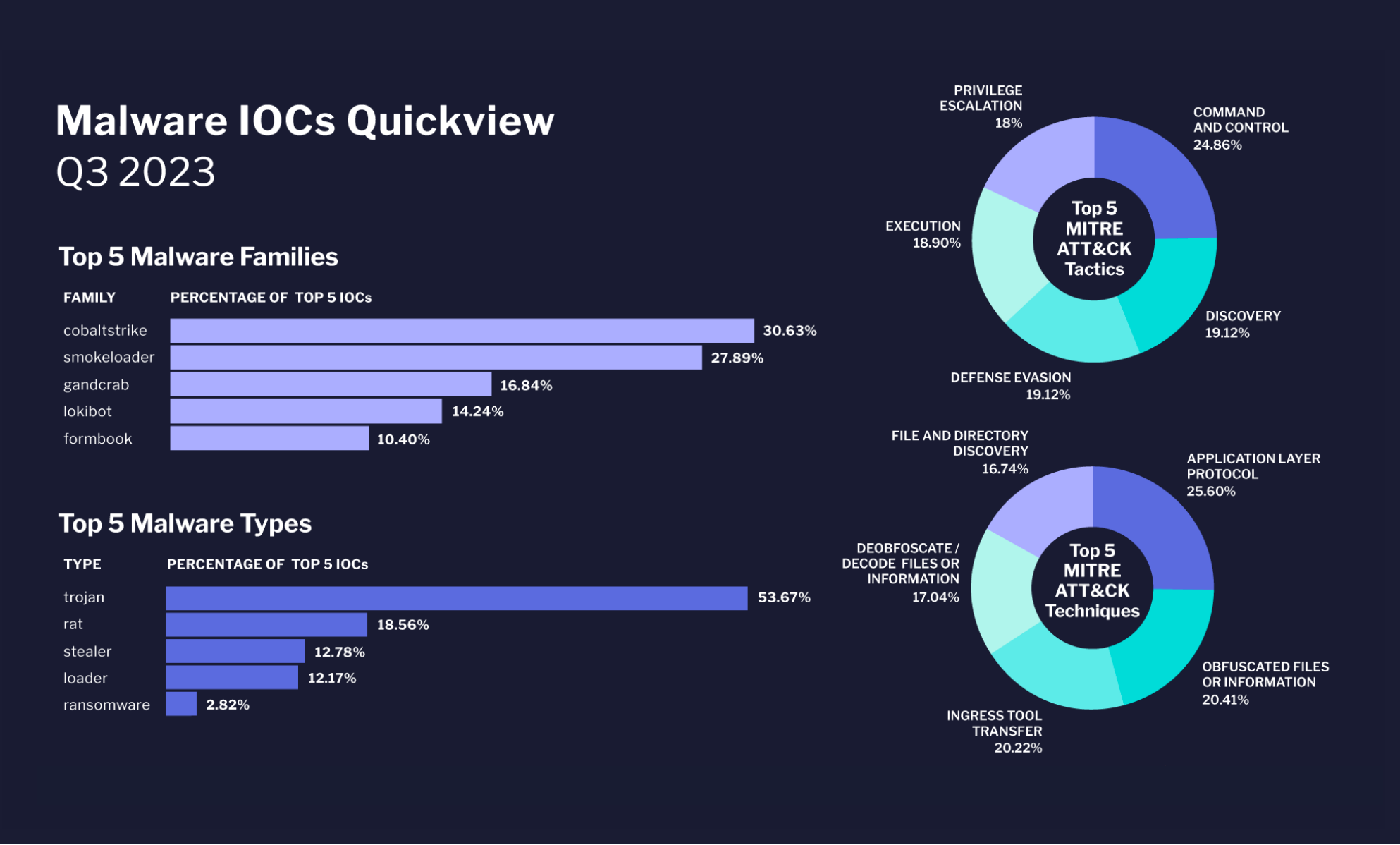
Top 5 Malware Families:
- CobaltStrike takes the lead, representing 30.63% of the top 5 Indicators of Compromise (IOCs).
- SmokeLoader follows at 27.89%.
- GandCrab is at 16.84%.
- Lokibot constitutes 14.24%.
- Formbook trails at 10.40%.
Top 5 Malware Types:
- Trojans are the most prevalent, accounting for 18.56% of the top 5 IOCs.
- RAT (Remote Access Trojan) comes next at 18.56%.
- Stealer type malware constitutes 12.78%.
- Loader represents 12.17%.
- Ransomware, while infamous, only accounts for 2.82% of the top 5 IOCs.
Top 5 MITRE ATT&CK Tactics:
- Command and Control is the predominant tactic at 24.86%.
- Application Layer Protocol is a close second at 25.60%.
- Discovery and Defense Evasion both hold equal proportions at 19.12% each.
- Execution is observed at 18.90%.
- Privilege Escalation accounts for 18%.
- File and Directory Discovery is at 16.74%.
Top 5 MITRE ATT&CK Techniques:
- A substantial 53.67% of the techniques involve Deobfuscating/Decoding files or information.
- Obfuscated Files or Information techniques account for 20.41%.
- Ingress Tool Transfer stands at 20.22%.
As we move into 2024, the threat posed by malware and security breaches remains ever-present and ever-evolving. In light of this, it is essential for individuals and organizations alike to proactively arm themselves against such threats. Here are key measures to ensure protection against the multifaceted landscape of cyber threats:
- Education and Awareness: Knowledge is the first line of defense. Stay informed about the latest threats and familiarize yourself with common phishing tactics. Regularly conducting cybersecurity training sessions can significantly reduce the chances of an inadvertent breach.
- Regular Software Updates: Ensure that all operating systems, applications, and antivirus software are up-to-date. Cyber attackers often exploit known vulnerabilities in outdated software.
- Multi-Factor Authentication (MFA): Implement MFA wherever possible. This adds an additional layer of security, making it significantly more challenging for attackers to gain unauthorized access.
- Backup Regularly: Maintain regular backups of essential data, stored both locally and in the cloud. This ensures data availability, even if hit by ransomware or other destructive malware.
- Firewalls and Antimalware Tools: Employ a robust firewall to monitor and control incoming and outgoing network traffic. Couple this with a reputable antimalware solution to scan, detect, and remove threats.
- Limit Access: Use the principle of least privilege (PoLP). Ensure that users and applications only have the access necessary to perform their tasks, reducing the potential damage of a breach.
- Secure Physical Access: Not all breaches are digital. Ensure that sensitive areas and systems are secured physically against unauthorized access.
- Regular Audits and Penetration Testing: Periodically assess the organization’s cybersecurity posture. Regular penetration testing can identify vulnerabilities before attackers do.
- Stay Updated with Patches: Vendors often release patches for known vulnerabilities. Applying these patches in a timely manner is crucial.
- Network Segmentation: By segmenting the network, an infection or breach in one segment can be contained, preventing it from spreading to other parts of the organization.
In conclusion, the approach to cybersecurity as we advance into 2024 must be holistic, encompassing technology, processes, and people. By fostering a culture of security awareness, combined with the implementation of advanced protective measures, we can navigate the digital age with greater confidence and resilience against the rising tide of cyber threats.
By Randy Ferguson