SSO is an acronym for Single Sign-On, a software program which uses one set of login credentials to gain entry to multiple applications. The average person maintained 27 passwords in 2016, an increase from 6.5 in 2007. In the most simple form, SSO is used by businesses to reduce the sheer amount of passwords employees are required to keep track of, but there is more to it than that.
Perhaps the most obvious benefit to SSO is at the user end. A singular password is easier to remember and alter compared to requiring a separate password per application. However, this benefit has a secondary perk as well — productivity. Entering one password saves time and ensures that working hours are used more efficiently.
The IT department also benefits from the use of SSO. IT departments report that 30% of help desk calls are related to password reset issues. One password entry saves the IT department time spent resetting employee passwords, allowing them to focus on more pressing matters. SSO allows IT to maintain user management and easily adjust accounts across various platforms.
When multiple passwords are required, unfavorable habits develop where employees keep each code simple (easy to remember) versions of their other passwords. This can lead to a security risk for business and is one way SSO is safer for Workplace security. However, SSO software may not be risk free.
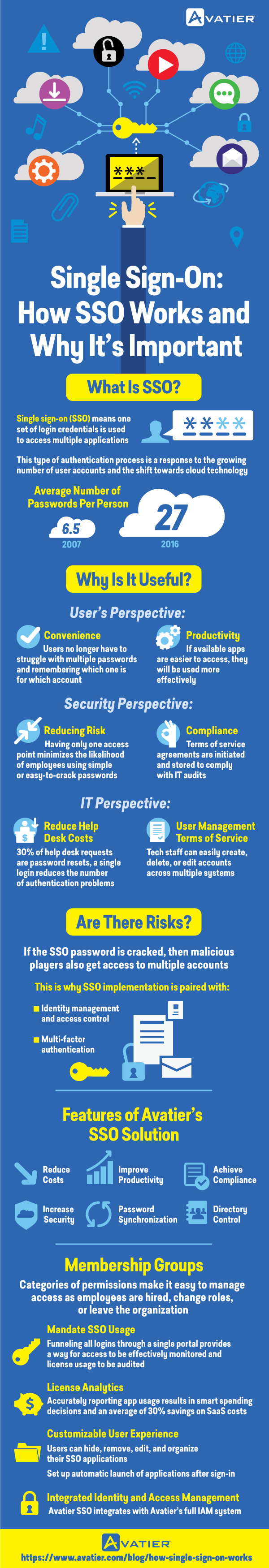
Like any password protected applications, SSO software is vulnerable to malicious activity or hackers. However, there are ways to keep applications under SSO software safe. Primarily, users should create unique passwords containing both numbers and letters as will as additional punctuation marks. Additionally, use multi-factor identification with the login. Multi-factored logins ensure that the user’s identity is confirmed and creates a secure system.
Convenience, productivity, and security are three great reasons to implement SSO software, but there are additional benefits to the service. Most importantly, SSO software is a part of compliance protocols. The software is able to initiate and store terms and service agreements, keeping the information safe and handy for IT audits. SSO Software options have additional features, such as analytics with app usage statistics and membership groups that allow different employee roles to have access to only the applications they require. Some software choices also offer customizable user experiences allowing users to organize what they see by removing, editing or hiding applications. Users are also able to set up most-used applications to open upon launching the software.
Personal lives have also seen the rise of SSO software in the form of using social media accounts as login for multiple websites, helping to reduce the amount of passwords we use at home as well. The perks of using single sign-on software for business far outweigh possible risk, especially considering the risk is manageable. In this online age where passwords are required everywhere, SSO saves time, money, and lowers frustration levels within the workplace. Using SSO software is a smart, business friendly solution to password overload.
By Oles Kosiuk





