Application dependencies are the external components, libraries, and frameworks that a software application requires in order to function correctly. These dependencies may include things like operating system libraries, third-party libraries, and other software applications that the application relies on in order to run.
For example, if an application is written in Python, it might have a dependency on the Python runtime environment and specific Python libraries. If the application is a web application, it might have dependencies on web servers, databases, and other web-based technologies.
It is important for developers to carefully manage application dependencies, as they can impact the performance and stability of the application. This may involve keeping track of which dependencies are used, ensuring that they are compatible with the application, and regularly updating them as needed.
When migrating an application to the cloud, it is important to carefully consider the dependencies of the application and how they will be impacted by the move. Some factors to consider include:
By carefully managing application dependencies during a cloud migration, it is possible to ensure that the application functions correctly and performs optimally in the cloud.

Version pinning involves specifying a specific version of a dependency that the application should use, rather than using the latest version or allowing the dependency to be automatically updated. This helps to ensure that the application and its dependencies are tested and known to work together, which can help prevent issues that may arise from using untested or incompatible versions of dependencies.
In the context of cloud migration, version pinning can be particularly important because it helps to ensure that the application and its dependencies are compatible with the cloud environment. By specifying a specific version of a dependency, developers can be confident that the application and its dependencies will work properly in the cloud, reducing the risk of issues arising after the migration.
When an application depends on external libraries or frameworks, it is important to ensure that these dependencies are not tampered with or modified in any way. Hash and signature verification can be used to verify the integrity of the dependencies by comparing a calculated hash or digital signature of the dependency with a known, trusted value. If the calculated hash or signature does not match the trusted value, it may indicate that the dependency has been tampered with or is not the intended version.
In the context of cloud migration, hash and signature verification can be particularly important because it helps to ensure that the application and its dependencies are not compromised in any way during the migration process. This can help to prevent issues that may arise from using tampered or compromised dependencies in the cloud.
Private dependencies are those that are developed and maintained internally within an organization, while public dependencies are those that are developed and maintained by external parties. Mixing private and public dependencies can introduce security vulnerabilities because it can be difficult to thoroughly vet and maintain the security of all of the dependencies being used by an application.
In the context of cloud migration, avoiding mixing private and public dependencies can be particularly important because it helps to ensure that the application and its dependencies are secure and compliant with the organization’s security policies. This can help to prevent security issues that may arise from using untested or potentially vulnerable dependencies in the cloud.
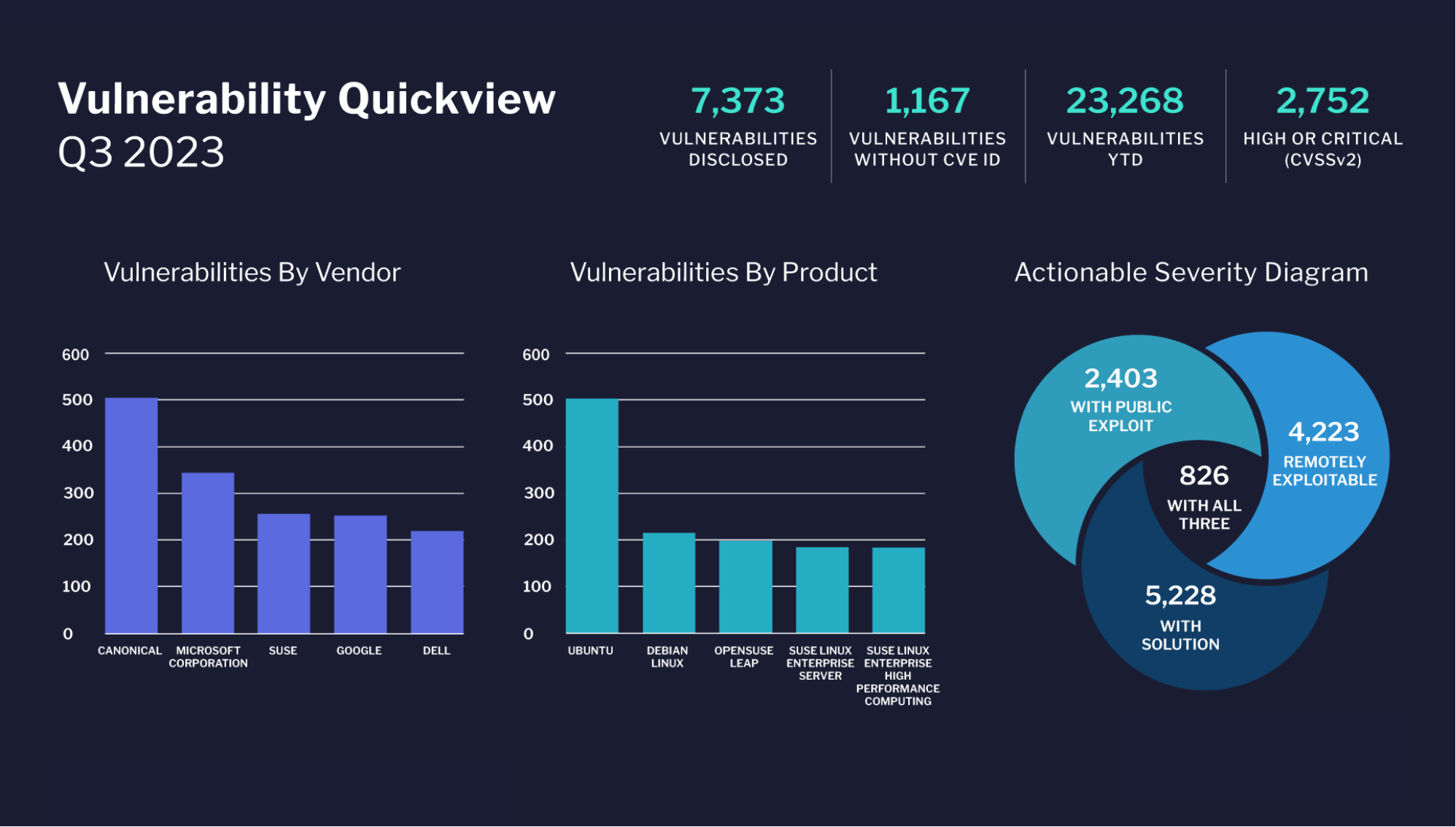
Vulnerability scanning involves using automated tools to scan the dependencies of an application for known vulnerabilities. This can help to identify vulnerabilities that may have been introduced through the dependencies and take steps to address them.
In the context of cloud migration, vulnerability scanning can be particularly important because it helps to ensure that the application and its dependencies are secure and compliant with the organization’s security policies. This can help to prevent security issues that may arise from using vulnerable dependencies in the cloud.
In conclusion, managing application dependencies is an important aspect of a successful cloud migration. Ensuring that the application and its dependencies are compatible with the cloud environment, properly configured and installed, and secure and compliant with the organization’s security policies can help to prevent issues that may arise during the migration process and ensure that the application performs as expected in the cloud.
Some best practices for managing application dependencies in a cloud migration include version pinning, hash and signature verification, avoiding the mixing of private and public dependencies, and vulnerability scanning. By following these best practices, organizations can effectively manage their application dependencies in a cloud migration and ensure a successful transition to the cloud.
Gilad David Maayan