Ransomware can bring your business to its knees. Whether it comes as a system- or network-wide infection, it can do a severe damage to your company.
Ransomware starts with malware that infects a system by using malicious software to take control of your computer, or even your entire network. The infection encrypts data then the attackers use the locked data as leverage.
Victims are told to pay money to have their data released.
The FBI discourages you from paying the ransom. Whether you do it or not, your data may be lost forever. According to recent research by Symantec, chances of having your files back after you pay the ransom are very slim. For more than half of companies, this never happens.
Given the trend, the best way to protect from ransomware is to keep your data safe and ensure it never happens.
Below are some of the best practices for preventing ransomware from entering your system or network.
An emailed virus can infect your entire system or network. It can be an attachment or a link in a phishing email, and you unknowingly activate it by downloading the attachment or clicking a link.
Once it is in your system, the active virus runs code on your system or network. The code encrypts your data so you can no longer access it and locks you out of your own system.
Be skeptical of your emails. If you are not familiar with a sender or the subject, do not open it. This will help you avoid phishing emails that may contain a virus.
Do not click links or open attachments which you are unsure of the source. Do not follow email prompts to “log in”. Instead, go to the website you are familiar with and log in from there.
There are many email settings available to reduce spam or questionable emails. You can stop email spoofing and phishing emails from reaching your inbox by turning on your spam filters.
In addition to this, you can use Macros. Macros automate everyday tasks in Microsoft office such as sending emails. Unfortunately, a Malware virus can be attached to the automated email. To prevent this, you should disable macro scripts from emailed office files.
Ransomware works by altering the code to lock your data.
This is where regular backups come in. Having a comprehensive cloud backup system or keeping regular offsite backups on an external drive can bring your data back in seconds.
If you are using hard drive backups, you should prepare your devices before you begin your backup. You will need to turn off all internet connections and online networks. As soon as the backup is complete, remove the external drive from your computer. Always store your external drive in a safe place that is not connected to the internet.
A more convenient option is cloud backup, which offers you much more flexibility. You choose a trusted vendor, find a suitable backup plan, and everything else will be done automatically from the cloud.
“If a virus reaches your system or network, you will need to restore your data back to its original state. You must have a current clean copy backed and available. I suggest a cloud based storage option as your data is stored offsite and secure.” said Ian McClarty CEO of phoenixNAP.
Wiping your system clean will remove the entire virus. Once your system is clean, you can restore your data. To restore your data, you will use your backed up data.
By regularly backing up your data, you will consistently have a current copy of your data. By having a current copy of your data, you will be able to restore your data quickly. This will drastically minimize your personal or business downtime.
You should follow best practices and back up your data in at least two separate offline locations.
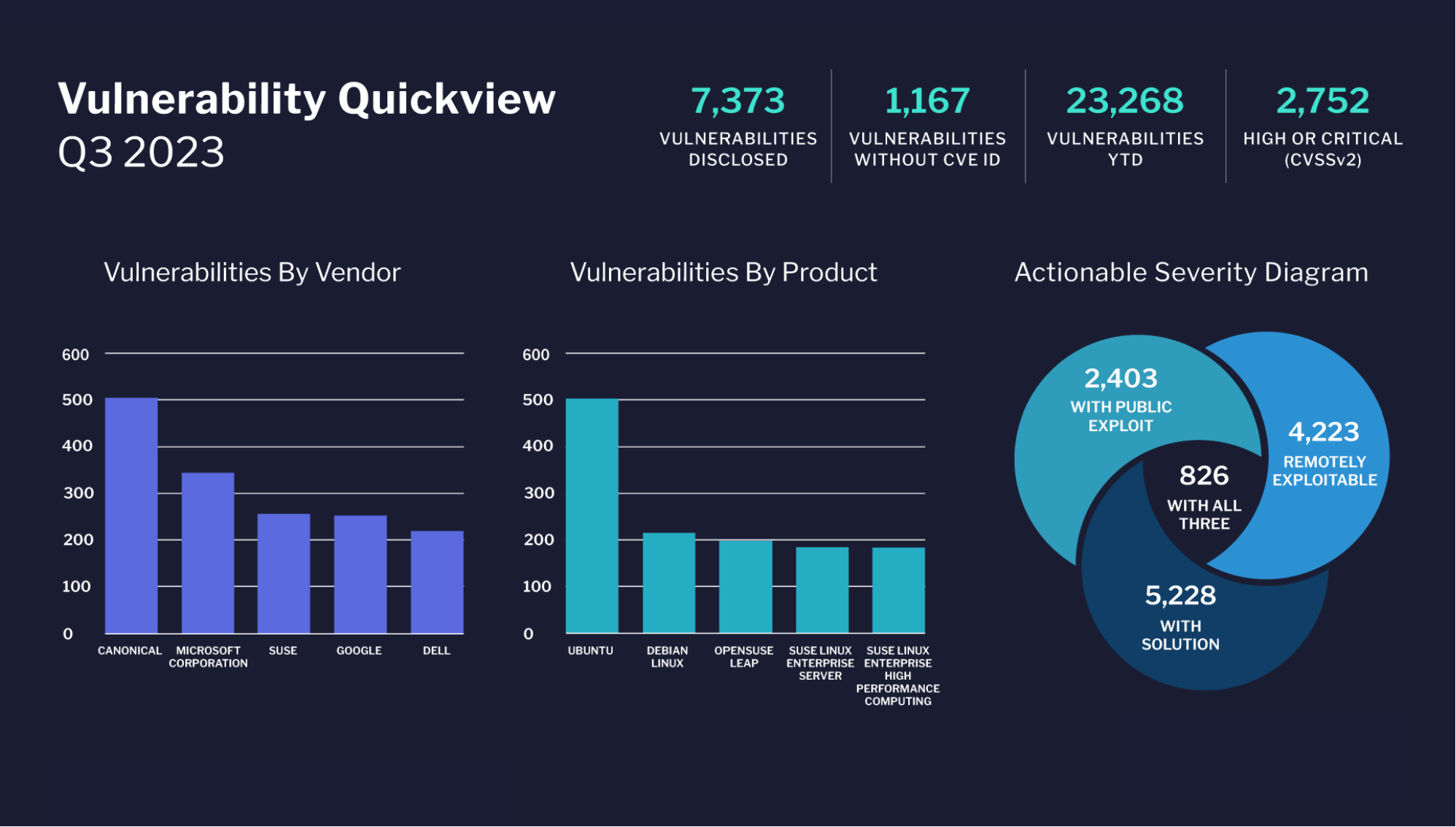
Maintaining up-to-date anti-virus software on all your devices is key to preventing breaches. With each system upgrade, the number of known Vulnerabilities reduces and hackers find it more difficult to access your system.
Change your software settings to conduct automatic scans and updates. If you perform a scan manually, remove all your external devices before you start the scan. This includes removing your mobile devices, USB drives, and CDs. To prevent viruses from reaching your computer, you should conduct manual scans on all software before you download it.
An active virus runs code (or patches) on your system or network. You should use a patch management system and set-up a regular patching routine. The patching routine will scan for weak codes in your system or network because weak codes can be easily acted on by a virus.
To be more protected from a malware attack, turn on your firewalls.
You may find yourself surprised if a virus attacks your computer while you are browsing the Internet. It is shocking if it happens to you, but a virus can easily reach your computer while you are on the web.
A virus can enter your system through social media messaging, email programs, or a poor web browser. You can also turn-on a virus by clicking on images and multimedia.
Use safe internet habits by being aware of what you are clicking on.
Careful clicking is an important part of keeping your data safe. Popups can bombard your screen and cause accidental clicks.
Turn on your popup blockers to prevent accidental clicks. Use a browser that has an ad-blocking plugin. You should consider using the web browsers Chrome or Firefox because they have potent ad blockers.
It is common for ransomware attacks to target businesses. For a business to do well, it must be steady. When a virus locks a business’s data, the business must stop and work is lost. Hackers assume that business owners will pay to unlock their business’s data so they can start work again.
Your business is at-risk to the common ways that viruses enter systems and networks. Your business should follow best practices to mitigate the risk of a cyber attack.
Educate your employees about online cyber threats. Be sure to explain the common ways that viruses can enter a system, such as emails, attachments, downloads, and web browsing. You should stress the importance of careful data management. If it can happen to a billion dollar company like UBER, it can happy to yours.
Like bio-viruses, computer viruses can have many strains.
Some virus strains only target admin accounts. To lessen the risks to your admin accounts, take precautions. Remove local admin rights, have few admin accounts, and only use admin accounts when you need to.
Other virus strains target certain tasks you do or actions you take on the computer. To lessen the risk of these strains, use your permissions settings to limit access to networks, directories, and files.
Cyber attacks target businesses and they must be prepared for them.
To quickly restore business, you need to have an incident response plan in place. The incident response plan is crucial for disaster recovery efforts.
In an attack, time is a critical factor. With an incident response plan in place, your team will be trained and ready to respond to the attack and perform disaster recovery. This will reduce the severity of damage to your business, systems, networks, and data.
The plan will describe the people who will respond, the policies and procedures they will follow, and the tools and skills they will need to do so. The incident response plan is an addition to your complete cybersecurity plan.
Verify: Are your Ransomware Prevention strategies being followed?
Like any emergency planning, you should check your plans, be sure they work, and consistently improve them. You should perform tests annually, if not more often, to be sure that your prevention tactics are working.
If you back up your data in real-time in the cloud, take extra precaution to secure your backups. Perform checks on the security of your systems more frequently.
If a virus attacks your data backup method, you may not be able to restore your data. Every time you back up your data, verify it is correctly copied and stored. You should also check your data restoration process to be sure it works.
Malware and viruses are constantly evolving. You should advance your incident response plan regularly to ensure effectiveness. Be sure to have frequent cyber attack drills. This will confirm that your team knows how to use the plan and that the plan works.
Your backups are only as strong as the drives and platforms you keep them on. By choosing the right solution for your needs, you have already made the first step to preventing ransomware. Follow the other suggested steps to bring the risk down to zero.
By Jessica Anderson